Database Activity Monitoring
Instant Threat Detection. Seamless Compliance Protection.
Gain real-time visibility into data usage, empowering you to detect, investigate, neutralize and report unauthorized access before it escalates into a threat.
Real-time Visibility and Control Over All Your Data
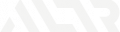
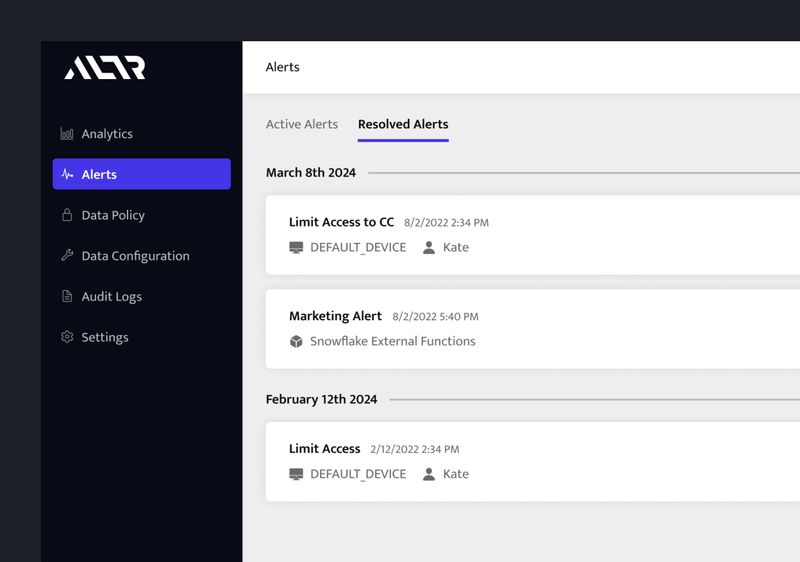
Real-Time Detection & Alerting
Immediately identify unauthorized data access or unusual behavior with ALTR’s real-time monitoring, providing instant alerts to your security teams for swift action.
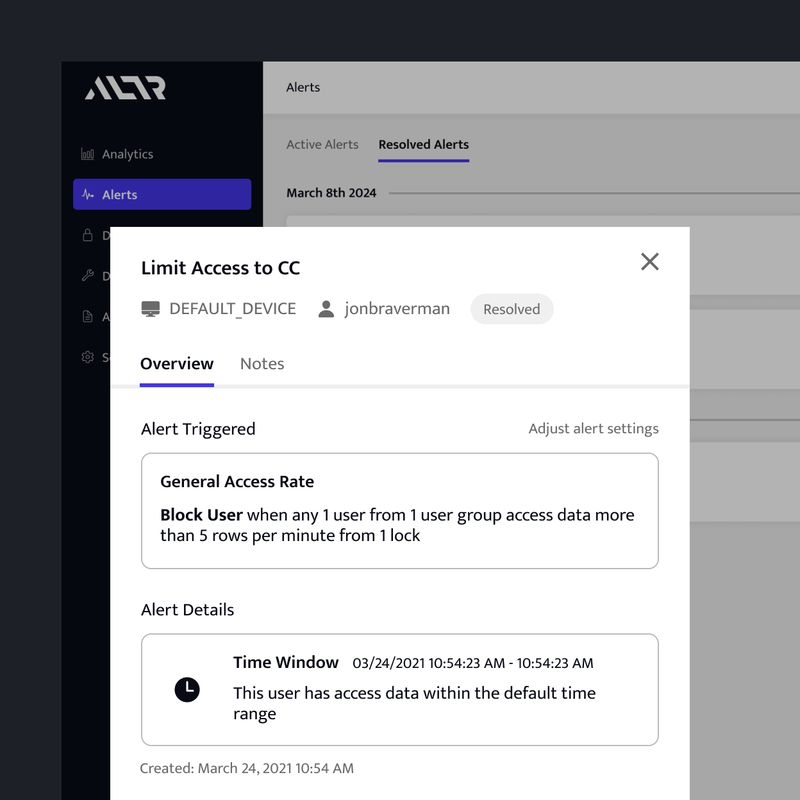
Automated Threat Blocking
Automatically block access when thresholds are violated or anomalies are detected, ensuring threats are neutralized before they escalate into breaches.
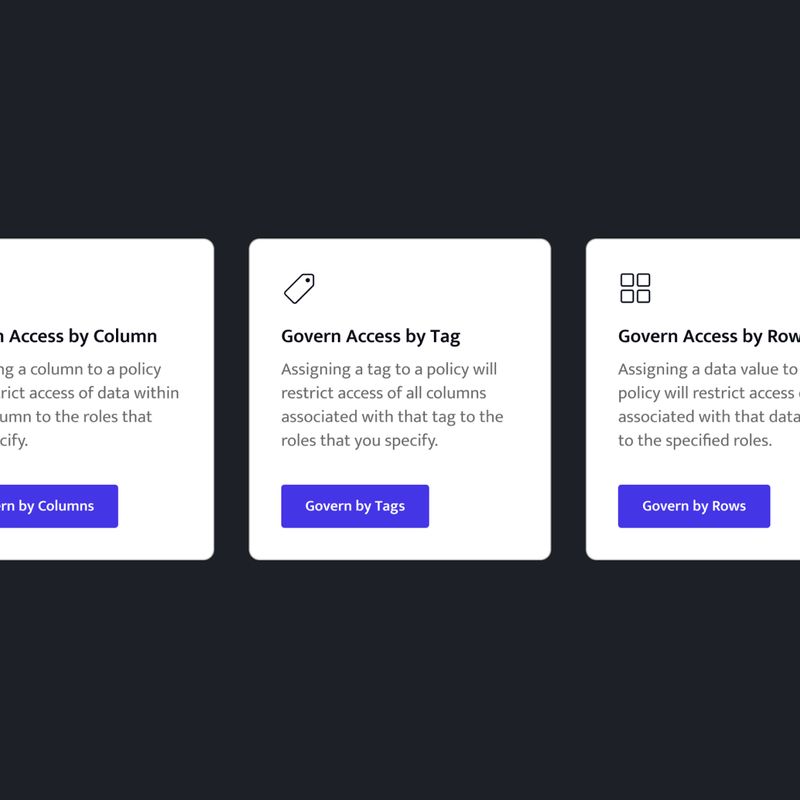
Policy-Based Access Controls
Set and enforce data access rules to prevent unauthorized access, leveraging roles, attributes, and policy-based controls to ensure comprehensive protection.
Comprehensive Audit Logs
Track every query and access attempt with detailed audit logs, giving you a complete record to support compliance requirements and incident investigations.
Data Usage Analytics
Analyze trends in data access and usage over time to uncover inefficiencies, identify risks, and fine-tune your security policies for maximum effectiveness.
SIEM Integration
Integrate ALTR seamlessly with your SIEM tools, enabling centralized threat detection and response workflows without additional complexity.
Get a Clear View of Data Access in Motion
ALTR’s Activity Monitoring Dashboard gives you a clear, real-time view of how your data is being accessed, who’s querying it, what they’re touching, and whether it aligns with your security policies. Visualize trends, investigate specific queries, and spot anomalies as they happen, all in one place, so your team can move from visibility to action without delay.
Proactive Threat Prevention
ALTR’s Database Activity Monitoring empowers security teams to stop threats before they impact sensitive data. This minimizes the risk of breaches, reduces incident response time, and enhances overall security posture.
Simplified Compliance Management
Comprehensive audit logs and precise access policies ensure security teams can meet regulatory requirements with ease. ALTR streamlines audit preparation and demonstrates robust data governance to regulators, reducing compliance stress and penalties.
Scalable Security
ALTR’s customizable policies and integration capabilities grow with your organization, allowing security teams to adapt security measures as the business scales or compliance requirements change, ensuring long-term resilience.
No Matter the Industry, Your Data Is Protected
Understanding and controlling how sensitive data is accessed, used, and protected is essential for maintaining security and compliance. ALTR’s Database Activity Monitoring (DAM) delivers real-time insights into user activity, detects anomalies, and enforces policies to prevent unauthorized access, ensuring the integrity of data across every industry.
Finance
Monitor and control access to sensitive financial data while generating compliance-ready audit logs.
Healthcare
Track every interaction with patient records and enforce strict access policies to prevent unauthorized data exposure.
Retail
Identify and block suspicious access patterns to protect payment systems and customer information in real time
Government
Enforce precise access limits and track usage with detailed logs to secure classified data and ensure compliance.
Just Ask Our Customers
A leading financial institution serving 11 million customers partnered with ALTR to meet strict regulatory requirements for real-time data governance. Using ALTR’s cloud-native integration and custom audit logging, the institution achieved comprehensive monitoring of sensitive data activities in Snowflake, enabling instant detection of unauthorized access.

Resources You Might Like
Frequently asked questions
What is database activity monitoring (DAM)?
Database Activity Monitoring (DAM) tracks and analyzes how data is accessed. It shows who accessed what, when, and how to detect risk and enforce security policies in real time.
What does database activity monitoring actually track?
ALTR tracks queries, users, roles, data accessed, timing, and access patterns—along with how data is protected by security policies.
How does ALTR monitor database activity?
ALTR sits in the query path and captures activity in near real time, logging who accessed data, what was accessed, and how it was used.
What makes ALTR’s database activity monitoring different?
ALTR combines visibility with enforcement, detecting suspicious activity and automatically blocking or restricting access based on policy.
Can ALTR detect and stop suspicious data access?
Yes. ALTR defines normal behavior, triggers alerts on anomalies, and can automatically block access based on unusual patterns like time, volume, or frequency.
Does ALTR provide real-time alerts?
Yes. ALTR delivers near real-time alerts when activity violates defined policies, enabling immediate investigation and response.
How does database activity monitoring support compliance?
DAM creates detailed, tamper-resistant audit trails that show how sensitive data is accessed and protected, helping meet standards like PCI DSS, HIPAA, and GDPR.
Eliminate Risk, Ensure Compliance.
Contact our Data Security Experts to secure your data, stay compliant, and tackle threats with confidence.