Format-Preserving Encryption: A Deep Dive into FF3-1 Encryption Algorithm




In the ever-evolving landscape of data security, protecting sensitive information while maintaining its usability is crucial. ALTR’s Format Preserving Encryption (FPE) is an industry disrupting solution designed to address this need. FPE ensures that encrypted data retains the same format as the original plaintext, which is vital for maintaining compatibility with existing systems and applications. This post explores ALTR's FPE, the technical details of the FF3-1 encryption algorithm, and the benefits and challenges associated with using padding in FPE.
Format Preserving Encryption is a cryptographic technique that encrypts data while preserving its original format. This means that if the plaintext data is a 16-digit credit card number, the ciphertext will also be a 16-digit number. This property is essential for systems where data format consistency is critical, such as databases, legacy applications, and regulatory compliance scenarios.
The FF3-1 encryption algorithm is a format-preserving encryption method that follows the guidelines established by the National Institute of Standards and Technology (NIST). It is part of the NIST Special Publication 800-38G and is a variant of the Feistel network, which is widely used in various cryptographic applications. Here’s a technical breakdown of how FF3-1 works:
1. Feistel Network: FF3-1 is based on a Feistel network, a symmetric structure used in many block cipher designs. A Feistel network divides the plaintext into two halves and processes them through multiple rounds of encryption, using a subkey derived from the main key in each round.
2. Rounds: FF3-1 typically uses 8 rounds of encryption, where each round applies a round function to one half of the data and then combines it with the other half using an XOR operation. This process is repeated, alternating between the halves.
3. Key Scheduling: FF3-1 uses a key scheduling algorithm to generate a series of subkeys from the main encryption key. These subkeys are used in each round of the Feistel network to ensure security.
4. Tweakable Block Cipher: FF3-1 includes a tweakable block cipher mechanism, where a tweak (an additional input parameter) is used along with the key to add an extra layer of security. This makes it resistant to certain types of cryptographic attacks.
5. Format Preservation: The algorithm ensures that the ciphertext retains the same format as the plaintext. For example, if the input is a numeric string like a phone number, the output will also be a numeric string of the same length, also appearing like a phone number.
1. Initialization: The plaintext is divided into two halves, and an initial tweak is applied. The tweak is often derived from additional data, such as the position of the data within a larger dataset, to ensure uniqueness.
2. Round Function: In each round, the round function takes one half of the data and a subkey as inputs. The round function typically includes modular addition, bitwise operations, and table lookups to produce a pseudorandom output.
3. Combining Halves: The output of the round function is XORed with the other half of the data. The halves are then swapped, and the process repeats for the specified number of rounds.
4. Finalization: After the final round, the halves are recombined to form the final ciphertext, which maintains the same format as the original plaintext.
Implementing FPE provides numerous benefits to organizations:
1. Compatibility with Existing Systems: Since FPE maintains the original data format, it can be integrated into existing systems without requiring significant changes. This reduces the risk of errors and system disruptions.
2. Improved Performance: FPE algorithms like FF3-1 are designed to be efficient, ensuring minimal impact on system performance. This is crucial for applications where speed and responsiveness are critical.
3. Simplified Data Migration: FPE allows for the secure migration of data between systems while preserving its format, simplifying the process and ensuring compatibility and functionality.
4. Enhanced Data Security: By encrypting sensitive data, FPE protects it from unauthorized access, reducing the risk of data breaches and ensuring compliance with data protection regulations.
5. Creation of production-like data for lower trust environments: Using a product like ALTR’s FPE, data engineers can use the cipher-text of production data to create useful mock datasets for consumption by developers in lower-trust development and test environments.
Padding is a technique used in encryption to ensure that the plaintext data meets the required minimum length for the encryption algorithm. While padding is beneficial in maintaining data structure, it presents both advantages and challenges in the context of FPE:
1. Consistency in Data Length: Padding ensures that the data conforms to the required minimum length, which is necessary for the encryption algorithm to function correctly.
2. Preservation of Data Format: Padding helps maintain the original data format, which is crucial for systems that rely on specific data structures.
3. Enhanced Security: By adding extra data, padding can make it more difficult for attackers to infer information about the original data from the ciphertext.
1. Increased Complexity: The use of padding adds complexity to the encryption and decryption processes, which can increase the risk of implementation errors.
2. Potential Information Leakage: If not implemented correctly, padding schemes can potentially leak information about the original data, compromising security.
3. Handling of Padding in Decryption: Ensuring that the padding is correctly handled during decryption is crucial to avoid errors and data corruption.
ALTR's Format Preserving Encryption, powered by the technically robust FF3-1 algorithm and married with legendary ALTR policy, offers a comprehensive solution for encrypting sensitive data while maintaining its usability and format. This approach ensures compatibility with existing systems, enhances data security, and supports regulatory compliance. However, the use of padding in FPE, while beneficial in preserving data structure, introduces additional complexity and potential security challenges that must be carefully managed. By leveraging ALTR’s FPE, organizations can effectively protect their sensitive data without sacrificing functionality or performance.
For more information about ALTR’s Format Preserving Encryption and other data security solutions, visit the ALTR documentation
For years (even decades) sensitive information has lived in transactional and analytical databases in the data center. Firewalls, VPNs, Database Activity Monitors, Encryption solutions, Access Control solutions, Privileged Access Management and Data Loss Prevention tools were all purchased and assembled to sit in front of, and around, the databases housing this sensitive information.
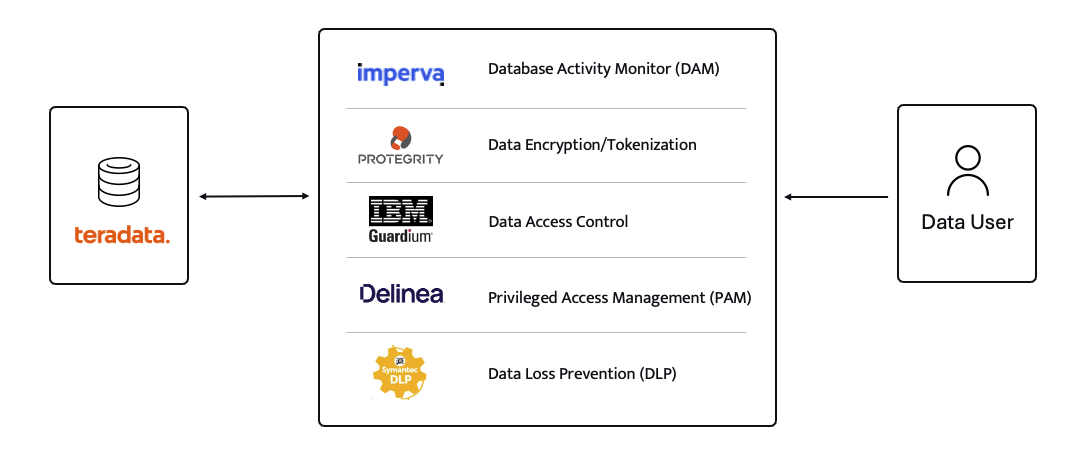
Even with all of the above solutions in place, CISO’s and security teams were still a nervous wreck. The goal of delivering data to the business was met, but that does not mean the teams were happy with their solutions. But we got by.
The advent of Big Data and now Generative AI are causing businesses to come to terms with the limitations of these on-prem analytical data stores. It’s hard to scale these systems when the compute and storage are tightly coupled. Sharing data with trusted parties outside the walls of the data center securely is clunky at best, downright dangerous in most cases. And forget running your own GenAI models in your datacenter unless you can outbid Larry, Sam, Satya, and Elon at the Nvidia store. These limits have brought on the era of cloud data platforms. These cloud platforms address the business needs and operational challenges, but they also present whole new security and compliance challenges.
ALTR’s platform has been purpose-built to recreate and enhance these protections required to use Teradata for Snowflake. Our cutting-edge SaaS architecture is revolutionizing data migrations from Teradata to Snowflake, making it seamless for organizations of all sizes, across industries, to unlock the full potential of their data.
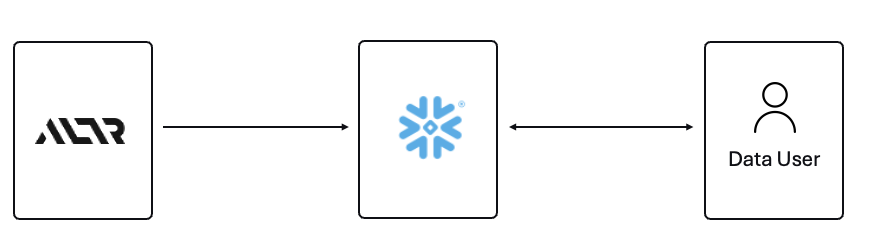
What spurred this blog is that a company reached out to ALTR to help them with data security on Snowflake. Cool! A member of the Data & Analytics team who tried our product and found love at first sight. The features were exactly what was needed to control access to sensitive data. Our Format-Preserving Encryption sets the standard for securing data at rest, offering unmatched protection with pricing that's accessible for businesses of any size. Win-win, which is the way it should be.
Our team collaborated closely with this person on use cases, identifying time and cost savings, and mapping out a plan to prove the solution’s value to their organization. Typically, we engage with the CISO at this stage, and those conversations are highly successful. However, this was not the case this time. The CISO did not want to meet with our team and practically stalled our progress.
The CISO’s point of view was that ALTR’s security solution could be completely disabled, removed, and would not be helpful in the case of a compromised ACCOUNTADMIN account in Snowflake. I agree with the CISO, all of those things are possible. Here is what I wanted to say to the CISO if they had given me the chance to meet with them!
The ACCOUNTADMIN role has a very simple definition, yet powerful and long-reaching implications of its use:
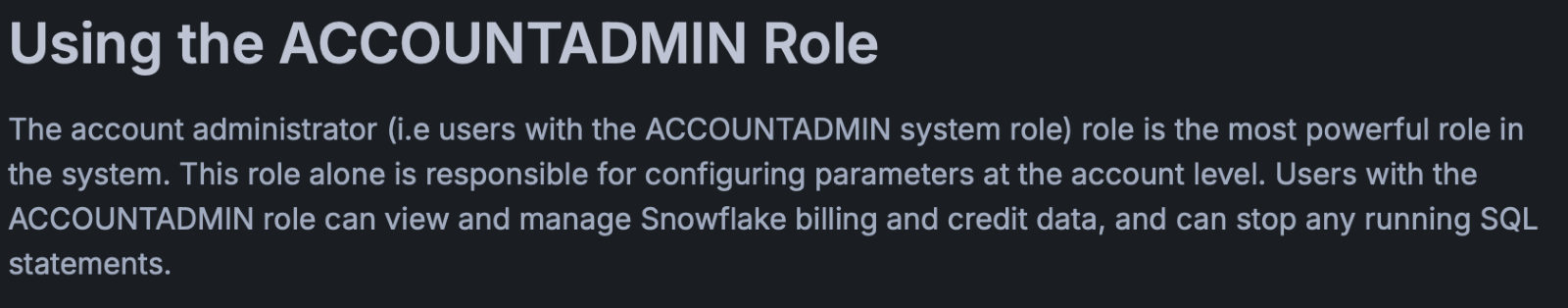
One of the main points I would have liked to make to the CISO is that as a user of Snowflake, their responsibility to secure that ACCOUNTADMIN role is squarely in their court. By now I’m sure you have all seen the news and responses to the Snowflake compromised accounts that happened earlier this year. It is proven that unsecured accounts by Snowflake customers caused the data theft. There have been dozens of articles and recommendations on how to secure your accounts with Snowflake and even a mandate of minimum authentication standards going forward for Snowflake accounts. You can read more information here, around securing the ACCOUNTADMIN role in Snowflake.
I felt the CISO was missing the point of the ALTR solution, and I wanted the chance to explain my perspective.
ALTR is not meant to secure the ACCOUNTADMIN account in Snowflake. That’s not where the real risk lies when using Snowflake (and yes, I know—“tell that to Ticketmaster.” Well, I did. Check out my write-up on how ALTR could have mitigated or even reduced the data theft, even with compromised accounts). The risk to data in Snowflake comes from all the OTHER accounts that are created and given access to data.
The ACCOUNTADMIN role is limited to one or two people in an organization. These are trusted folks who are smart and don’t want to get in trouble (99% of the time). On the other hand, you will have potentially thousands of non-ACCOUNTADMIN users accessing data, sharing data, screensharing dashboards, re-using passwords, etc. This is the purpose of ALTR’s Data Security Platform, to help you get a handle on part of the problem which is so large it can cause companies to abandon the benefits of Snowflake entirely.
There are three major issues outside of the ACCOUNTADMIN role that companies have to address when using Snowflake:
1. You must understand where your sensitive is inside of Snowflake. Data changes rapidly. You must keep up.
2. You must be able to prove to the business that you have a least privileged access mechanism. Data is accessed only when there is a valid business purpose.
3. You must be able to protect data at rest and in motion within Snowflake. This means cell level encryption using a BYOK approach, near-real-time data activity monitoring, and data theft prevention in the form of DLP.
The three issues mentioned above are incredibly difficult for 95% of businesses to solve, largely due to the sheer scale and complexity of these challenges. Terabytes of data and growing daily, more users with more applications, trusted third parties who want to collaborate with your data. All of this leads to an unmanageable set of internal processes that slow down the business and provide risk.
ALTR’s easy-to-use solution allows Virgin Pulse Data, Reporting, and Analytics teams to automatically apply data masking to thousands of tagged columns across multiple Snowflake databases. We’re able to store PII/PHI data securely and privately with a complete audit trail. Our internal users gain insight from this masked data and change lives for good.
- Andrew Bartley, Director of Data Governance
I believed the CISO at this company was either too focused on the ACCOUNTADMIN problem to understand their other risks, or felt he had control over the other non-admin accounts. In either case I would have liked to learn more!
There was a reason someone from the Data & Analytics team sought out a product like ALTR. Data teams are afraid of screwing up. People are scared to store and use sensitive data in Snowflake. That is what ALTR solves for, not the task of ACCOUNTADMIN security. I wanted to be able to walk the CISO through the risks and how others have solved for them using ALTR.
The tools that Snowflake provides to secure and lock down the ACCOUNTADMIN role are robust and simple to use. Ensure network policies are in place. Ensure MFA is enabled. Ensure you have logging of ACCOUNTADMIN activity to watch all access.
I wish I could have been on the conversation with the CISO to ask a simple question, “If I show you how to control the ACCOUNTADMIN role on your own, would that change your tone on your teams use of ALTR?” I don’t know the answer they would have given, but I know the answer most CISO’s would give.
Nothing will ever be 100% secure and I am by no means saying ALTR can protect your Snowflake data 100% by using our platform. Data security is all about reducing risk. Control the things you can, monitor closely and respond to the things you cannot control. That is what ALTR provides day in and day out to our customers. You can control your ACCOUNTADMIN on your own. Let us control and monitor the things you cannot do on your own.

Since 2015 the migration of corporate data to the cloud has rapidly accelerated. At the time it was estimated that 30% of the corporate data was in the cloud compared to 2022 where it doubled to 60% in a mere seven years. Here we are in 2024, and this trend has not slowed down.
Over time, as more and more data has moved to the cloud, new challenges have presented themselves to organizations. New vendor onboarding, spend analysis, and new units of measure for billing. This brought on different cloud computer-related cost structures and new skillsets with new job titles. Vendor lock-in, skill gaps, performance and latency and data governance all became more intricate paired with the move to the cloud. Both operational and transactional data were in scope to reap the benefits promised by cloud computing, organizational cost savings, data analytics and, of course, AI.
The most critical of these new challenges revolve around a focus on Data Security and Privacy. The migration of on-premises data workloads to the Cloud Data Warehouses included sensitive, confidential, and personal information. Corporations like Microsoft, Google, Meta, Apple, Amazon were capturing every movement, purchase, keystroke, conversation and what feels like thought we ever made. These same cloud service providers made this easier for their enterprise customers to do the same. Along came Big Data and the need for it to be cataloged, analyzed, and used with the promise of making our personal lives better for a cost. The world's population readily sacrificed privacy for convenience.
The moral and ethical conversation would then begin, and world governments responded with regulations such as GDPR, CCPA and now most recently the European Union’s AI Act. The risk and fines have been in the billions. This is a story we already know well. Thus, Data Security and Privacy have become a critical function primarily for the obvious use case, compliance, and regulation. Yet only 11% of organizations have encrypted over 80% of their sensitive data.
With new challenges also came new capabilities and business opportunities. Real time analytics across distributed data sources (IoT, social media, transactional systems) enabling real time supply chain visibility, dynamic changes to pricing strategies, and enabling organizations to launch products to market faster than ever. On premise applications could not handle the volume of data that exists in today’s economy.
Data sharing between partners and customers became a strategic capability. Without having to copy or move data, organizations were enabled to build data monetization strategies leading to new business models. Now building and training Machine Learning models on demand is faster and easier than ever before.
To reap the benefits of the new data world, while remaining compliant, effective organizations have been prioritizing Data Security as a business enabler. Format Preserving Encryption (FPE) has become an accepted encryption option to enforce security and privacy policies. It is increasingly popular as it can address many of the challenges of the cloud while enabling new business capabilities. Let’s look at a few examples now:
Real Time Analytics - Because FPE is an encryption method that returns data in the original format, the data remains useful in the same length, structure, so that more data engineers, scientists and analysts can work with the data without being exposed to sensitive information.
Data Sharing – FPE enables data sharing of sensitive information both personal and confidential, enabling secure information, collaboration, and innovation alike.
Proactive Data Security– FPE allows for the anonymization of sensitive information, proactively protecting against data breaches and bad actors. Good holding to ransom a company that takes a more proactive approach using FPE and other Data Security Platform features in combination.
Empowered Data Engineering – with FPE data engineers can still build, test and deploy data transformations as user defined functions and logic in stored procedures or complied code will run without failure. Data validations and data quality checks for formats, lengths and more can be written and tested without exposing sensitive information. Federated, aggregation and range queries can still run without fail without the need for decryption. Dynamic ABAC and RBAC controls can be combined to decrypt at runtime for users with proper rights to see the original values of data.
Cost Management – While FPE does not come close to solving Cost Management in its entirety, it can definitely contribute. We are seeing a need for FPE as an option instead of replicating data in the cloud to development, test, and production support environments. With data transfer, storage and compute costs, moving data across regions and environments can be really expensive. With FPE, data can be encrypted and decrypted with compute that is a less expensive option than organizations' current antiquated data replication jobs. Thus, making FPE a viable cost savings option for producing production ready data in non-production environments. Look for a future blog on this topic and all the benefits that come along.
FPE is not a silver bullet for protecting sensitive information or enabled these business use cases. There are well documented challenges in the FF1 and FF3-1 algorithms (another blog on that to come). A blend of features including data discovery, dynamic data masking, tokenization, role and attribute-based access controls and data activity monitoring will be needed to have a proactive approach towards security within your modern data stack. This is why Gartner considers a Data Security Platform, like ALTR, to be one of the most advanced and proactive solutions for Data security leaders in your industry.
Securing sensitive information is now more critical than ever for all types of organizations as there have been many high-profile data breaches recently. There are several ways to secure the data including restricting access, masking, encrypting or tokenization. These can pose some challenges when using the data downstream. This is where Format Preserving Encryption (FPE) helps.
This blog will cover what Format Preserving Encryption is, how it works and where it is useful.
Whereas traditional encryption methods generate ciphertext that doesn't look like the original data, Format Preserving Encryption (FPE) encrypts data whilst maintaining the original data format. Changing the format can be an issue for systems or humans that expect data in a specific format. Let's look at an example of encrypting a 16-digit credit card number:
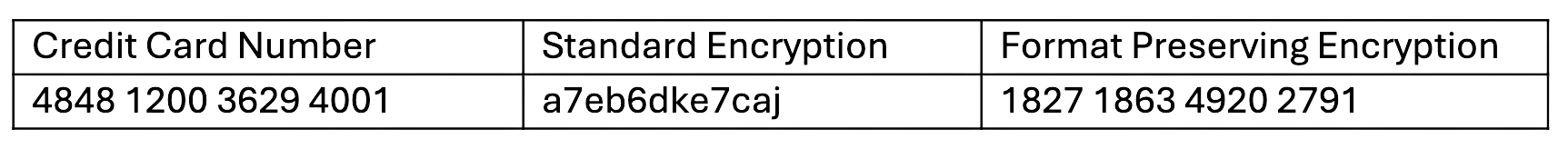
As you can see with a Standard Encryption type the result is a completely different output. This may result in it being incompatible with systems which require or expect a 16-digit numerical format. Using FPE the encrypted data still looks like a valid 16-digit number. This is extremely useful for where data must stay in a specific format for compatibility, compliance, or usability reasons.
Format Preserving Encryption in ALTR works by first analyzing the column to understand the input format and length. Next the NIST algorithm is applied to encrypt the data with the given key and tweak. ALTR applies regular key rotation to maximize security. We also support customers bringing their own keys (BYOK). Data can then selectively be decrypted using ALTR’s access policies.
FPE offers several benefits for organizations that deal with structured data:
1. Adds extra layer of protection: Even if a system or database is breached the encryption makes sensitive data harder to access.
2. Original Data Format Maintained: FPE preserves the original data structure. This is critical when the data format cannot be changed due to system limitations or compliance regulations.
3. Improves Usability: Encrypted data in an expected format is easier to use, display and transform.
4. Simplifies Compliance: Many regulations like PCI-DSS, HIPAA, and GDPR will mandate safeguarding, such as encryption, of sensitive data. FPE allows you to apply encryption without disrupting data flows or reporting, all while still meeting regulatory requirements.
FPE is widely adopted in industries that regularly handle sensitive data. Here are a few common use cases:
ALTR offers various masking, tokenization and encryption options to keep all your Snowflake data secure. Our customers are seeing the benefit of Format Preserving Encryption to enhance their data protection efforts while maintaining operational efficiency and compliance. For more information, schedule a product tour or visit the Snowflake Marketplace.

Growing up in Austin, I’ve been steeped in technology from the start – we were either talking about tech, music, or BBQ basically. And one of the things I heard was that “every company is a software company.” It apparently originated in Watts S. Humphrey’s book, Winning with Software: An Executive Strategy, but was repeated in 2015 by Microsoft CEO Satya Nadella. The idea was really simple: use software to spend less money and/or make more money. Companies wanted to find the most cost-effective source materials, track orders more efficiently, or use the web to reach more customers to increase sales.
Today we’re hearing a new mantra: every company is supposed to be a “data-driven company”. But this is a more difficult transition that requires we overcome new regulatory roadblocks. Luckily, we have a winning strategy from the past to guide us.
There weren’t really any external barriers to becoming “software companies.” Companies just had to hire people who could create software, and they were off and running. The only real limit was knowledge about what software could do and the number of people available who could write the code. Some industries including financial, healthcare and tech were well ahead of this technology curve. But other industries like consumer goods or manufacturing had to catch up. This created a “skills gap” that initially forced companies to hire expensive consultants to come in, evaluate the business, tell them where technology could improve service or increase sales, scope the technology needed, and then deliver it. This might help a company make more money in the long run or increase efficiencies in certain areas, but it certainly wasn’t quick or cheap.
Companies eventually overcame this hurdle with the advent of low-code or no-code tools — basically software that could do the code writing for users. WYSIWYG (what you see is what you get) tools like WIX or Squarespace for websites are one example. Before these self-service tools, company websites were owned and managed by the IT group because they required server set up and Java and HTML code to create and manage. Once these easy-to-use tools rolled out, employees across the enterprise gained the power that only coders and developers had before. The people who own making that part of the business more modern could do it themselves with these tools, creating an inflection point in technology adoption. The marketing team could now manage their own website, and a typo on the home page no longer had to be a major crisis.

The next generation of this idea is that “every company is a data-driven company” — it’s the latest strategy for companies to make more money or save more money. It makes sense — after companies developed and rolled out all that software, they started ingesting and generating a ton of data about the business and their customers. Companies now have personal information on millions of users, data on how those users use their software, where, when and how. Software also collected digital healthcare data, financial data, purchasing data, logistics data, mobile data, Internet of Things data. Just about everything that exists today – person or object – could have data associated with it that is collected and stored.
While companies are racing to optimize and monetize this amazing resource with technology to uncover insights and share those across the business, they face a new headwind they didn’t in the transition to becoming a software company: data privacy regulations. There were no regulations around writing code, but seemingly every month more and more laws come out directing how PII, PHI, and PCI data can be stored and shared. The E.U.’s GDPR data privacy law went into effect in 2018, California’s CCPA in 2020 and, this year, Virginia and Colorado passed regulations that protect consumer privacy. These regulations come with steep penalties for data leaks or misuse—California’s privacy act fines, for example, can range from $2,500 to $7,500 per record.
Overcoming this headwind means putting something in place to comply with these regulations. Like the industries that started behind in the transition to becoming a software company, many companies today may be early in their journey to data governance – according to TDWI research just 25% have a data governance program and 44% are only in the design phase. The rest aren’t even thinking about it yet. And they face a similar skills gap. Several of today’s governance technologies are based on legacy infrastructure that not only involve big investments in time, money, and human resources to implement, but also require expensive developers to set up and maintain. Because, guess what, just like the early days of software, they need people who can code!
The good news is that we already know the solution to that challenge: create no-code/low-code tools that allow non-coders to rollout and manage the data governance solution themselves. This is where ALTR is ahead of the curve. Our cloud-based data access control and security platform requires no code to set up or maintain. Any user can easily automate policy enforcement with a few clicks in the ALTR interface, immediately see how sensitive data is being consumed, and document that access and usage to comply with all relevant privacy regulations. No one needs to know SnowSQL, Apache Ranger, YAML or any other code – the activation of governance policies and controls can be handed off to the data governance teams or any other non-coders to implement and manage. Not only does the process become faster, it becomes less error prone. Governance teams can see that the policies are working correctly with their own eyes, and they can adjust immediately if there’s something off – just like a marketing team can fix a typo on their website.

By delivering data control and protection solutions that anyone can use, we’re allowing data governance to be self-service and enabling companies to utilize sensitive data because anyone can implement the necessary controls and protections.
And now with our ALTR Free (forever) plan, we’re truly democratizing data governance: we’re removing all the skills, expense or resource roadblocks standing in the way, so that everyone can control and protect data their data easily, swiftly and freely. Companies can turn the headwind into a tailwind to more quickly get more value out of data and become the “data-driven companies” they need to be.


The concept of “digital transformation” must be familiar to just about everyone in the business world at this point. Our applications and activities continue their migration from on-premises into the cloud at a rapid rate. With this comes the idea of “digital data transformation”. Data isn’t just moved as is, but should be re-imagined, remodeled and modernized to get the most from the cloud data platforms that will be hosting it.
To this end, ALTR has partnered with emerging digital data transformation firm DataSwitch.
DataSwitch's no-code and low-code platform along with cloud data expertise and unique, automated schema generation accelerate time to market. DataSwitch provides an end-to-end data, schema and ETL process migration with automated re-platforming and refactoring, thereby delivering faster time to market and significant reduction in cost of migration.
The DataSwitch Migrate toolkit leverages advanced automation to migrate schema, data, and processes from legacy databases like Oracle, Teradata, Netezza, and SQL server and ETL tools like Informatica, Datastage, and SSIS to modern cloud-based data warehouses like AWS Redshift, Snowflake, and Google BigQuery and integration platforms like Databricks, Spark, SnapLogic, and Matillion, etc. And all this is delivered with built-in technology best practices.
DS Migrate automates data transformation by implementing three key components which include:
With the full suite of DataSwitch tools, enterprises can scale their decision-making, automate manual processes, and simplify complex analyses, thereby accelerating time to translate data into real-world insights and build their scalable Cloud Data Platforms.
Furthermore, with experience dealing with the regulated industries DataSwitch in collaboration with ALTR is investing in domain-specific solution use cases to address needs which include business process automation, customer 360, institutional and market risk identification, and fraud detection.

For customers with sensitive data, migration to the cloud can be a little trickier due to privacy regulations. Integrating the DS Migrate toolkit with ALTR helps companies comply with the relevant rules through seamless tokenization of sensitive data as it is migrated, protecting it from risk of theft or leaks. Sensitive datasets of structured, semi-structured, and unstructured data can be tokenized without complex and lengthy software installation. There are no keys to maintain, and no maps to reduce the security of the data. And using ALTR’s cloud platform, tokenized data can be accessed from anywhere you allow. With ALTR, privacy, risk, compliance, data, and security teams work together to govern and automatically control access to sensitive data, simplifying role management, and ensuring data flows to whoever needs it while private information stays protected.
By combining ALTR and DataSwitch, data engineering teams can quickly and easily modernize their data architecture, migrate sensitive data to cloud data platforms safely, and share data with anyone who needs it while ensuring data privacy and security.


In just seven months since we launched our integration with Snowflake to deliver the market’s first cloud-native platform for observability, governance and protection of sensitive data, we’ve seen tremendous growth. We released innovative product features including automated data usage visualizations, launched the data governance industry’s first and only Free plan available via Snowflake Partner Connect, and seen significant customer momentum. And now we’re pleased to announce that the work we put into developing our Snowflake practice has resulted in ALTR attaining Premier Partner status in the Snowflake Partner Network.
We designed our solution for Snowflake to make it easy for enterprises of all sizes to take full advantage of the Snowflake platform. With our no-code, cloud-based solution, utilizing Snowflake’s native governance and security features, companies can enjoy enterprise-level data control and protection that is easy to implement and easy to manage and maintain, ensuring that valuable sensitive data can be both utilized across the business while staying secure.
Shared customers like innovative functional nutrition and supplement supplier, HumanN, are reaping the rewards. The consumer goods company utilizes Snowflake as a central database to analyze customer data from a multitude of cloud and on-premises systems. Adding ALTR allowed HumanN to include sensitive customer data into its analytics while ensuring the data is safe and in compliance with privacy regulations.
“Everything we do at HumanN is driven by our desire to help people—to push harder, to achieve greater and finish stronger,” said Kocher. “We treat our customers’ data with the same respect we treat the humans behind the data. Our adoption of ALTR is another step in that direction.”
Award-winning consumer activation company, Welltok is also seeing the benefits of being an ALTR/Snowflake customer. “Data security and privacy is of the utmost importance to Welltok and our clients, especially when it comes to health information,” said David MacLeod, CIO and CISO for Welltok. “Working with ALTR helps us ensure safety with real-time monitoring and action.”
Get started with the industry’s leading data control and protection solution for Snowflake. Get ALTR Free!


Last week, ALTR CTO and co-founder James Beecham had a Zoom call with Angelbeat’s Ron Gerber to chat about some data-related themes like the complexity of data, why data is becoming the new endpoint when you think about security, how PII is becoming the new PCI, and the challenges around using and securing sensitive data in your cloud data platform. Those themes and more are featured in the above video by way of preparing for the upcoming Angelbeat Data event in June (more to come on that soon).

Speaking of events, they’re a pretty big deal for us at ALTR; with all the knowledge sharing and networking, they’re mutually beneficial for vendors and attendees alike. From webinars and virtual events to the long-lost in-person trade shows, we consider ourselves fortunate to be able to work with folks like Ron Gerber of Angelbeat, our customers over at Q2, partners at Snowflake, and all the other experts who share their experiences and insight into the data security space.
In addition to speaking with Ron, James also recently hosted a webinar on “A Security-First Approach to Re-Platforming Data in the Cloud” with Q2’s CAO, Lou Senko, and Snowflake’s Head of Cyber Security, Omer Singer. This webinar not only demonstrates ALTR’s cloud integration with ALTR, but it also provides real use cases from our customer Q2.
On top of the availability of our Snowflake integration (used by Q2, The Zebra, and HumanN to name a few), we are excited to announce our latest integration with OneTrust. OneTrust unifies data governance under one platform, streamlining business processes and ensuring privacy and security practices are built-in to your data governance program.
Together, the integration between OneTrust and ALTR further simplifies data governance by automating the enforcement of governance policy. Now organizations can automatically and continuously discover, classify, and govern access to sensitive data. Sign up here to see a live demonstration of this integration on May 12th.
Along with periodic webinars with industry experts, customers, and partners, we’re also pleased to let you know that we will be participating in Dataversity’s 25th Annual Enterprise Data World event at the end of April as well as RSA’s annual conference in May. As life starts to get closer and closer to normal, we can’t wait to start seeing you all out at in-person conferences later in the year.
To keep up with all the events going on at ALTR, check out our events page, which is always up-to-date with where you can find us. If you are ready to get started with ALTR, you can try it for free or request a demo.

ALTR teamed up with IDG to host a discussion entitled Data, Security and Visibility: How to Minimize Risk in a Time of Rapid Business Change. The aim was to share best practices and challenges around:
With participants from an array of different industries, job functions, and project priorities, it was interesting to learn about their specific goals and challenges, but in the end it was evident that the group had a lot more in common than we anticipated.
One participant pointed out that whenever someone needs data within the company, they ask IT. While that seems like a logical place to start, it’s usually the business that actually owns and understands the data. While they usually end up finding it (from the business), it is not an efficient use of time and resources. The first step to solving this problem find a single platform to bridge that gap, providing observability and logging all consumption. This will allow IT to maintain protection of the data while also being able to curate it in a timely manner.
A member of the group shared his story of when the pandemic started and work from home became mandatory. Remote access, which for many organizations might have been a small percentage of their work force, suddenly became the only way that workers were using the organization’s resources. Strong network-focused security postures needed to adjust overnight into more data-centric approaches.
This conclusion came out of a discussion around security tools canceling out many of the reasons to leverage the cloud in the first place. Easy to get started, no hardware to install, and the ability to scale quickly are what make the cloud so appealing. So why shouldn’t your security solutions work the same way?
Many newer, more advanced security products are less bound to a specific infrastructure, which means that they can function across hybrid environments and simplify the complex mix of products. This simplification driven by the cloud has become a priority for security leaders.
Cloud data platforms have dramatically improved the speed, efficiency, and flexibility of collecting and analyzing data to power the modern data-driven enterprise. But ease of use and greater access to collected data has presented new challenges in terms of managing data consumption. The modern data ecosystem starts with core applications that create and use massive amounts of data every day. Along the way data is shared, both inbound data from third party sources and outbound data shared with close partners.
By first observing data consumption you can understand how data is being consumed to understand patterns and create baselines. It also reveals high risk applications that you should probably focus on. Once you understand how the data is being consumed can begin to actual govern the consumption. Using this approach, you ensure your data is safe while keeping it accessible for the business to do their jobs.
One attendee at the round table worked at a design firm that deals in very large files that are sensitive because they contain important intellectual property, while another worked for a large insurance company that deals with large structured databases that contain PII. Every organization has unique need and challenges, but they have all been affected by remote work and now have data traversing the Internet far more than before.

It’s January - the time of year when we kick off our New Year’s resolutions. One of the most common is “getting in shape”, and that often means signing up for a gym membership. In fact, about 12% of all gym memberships happen in January, according to the IHRSA. However, 50% of those new members quit within 6 months!
This year, why not consider beefing up your data governance and security program with ALTR instead?
3 ways the ALTR Free plan is better than a gym membership:
Obviously. But it’s free with no strings attached. Unlike some gym memberships, there’s no bait and switch. There’s no credit card required, there’s no limited time offer, there’s no 6-month trial rate – ALTR Free is free for life. You can use it as long as you want, upgrade if or when you’re ready, or stay on the free plan forever.
In fact, with ALTR there’s no contract at all. We’ve worked hard to make sure that our free version provides a complete data control and protection on its own. If you don’t find it’s providing the functionality you need, we hope you’ll let us know so we can improve. But if it’s just not doing it for you, you can quit at any time. Unlike the gym, you won’t have to send a notarized letter, certified mail to the company’s headquarters and then watch and wait to see if this is the month they stop debiting your account!
Depending on the shape you’re in, beginning a workout program can be intimidating. Maybe you’re not sure where to start, you don’t know how to use the machines, you’re worried you’ll be judged, or don’t want to deal with Instagram influencers recording their workouts while you’re just trying to burn off holiday calories! It can be the same with a data governance program. The idea may be so overwhelming you think you need 6 months to even figure out what data you should protect and where it is, before you can even think about launching your program.
With ALTR, it’s simple to get started. There’s no big set up, no long implementation project, no coding knowledge necessary. There’s no hardware to purchase and no consultants needed.
You can sign up directly through Snowflake Partner Connect or here on our site, connect your databases, discover and classify data instantly, choose the columns of sensitive data you want to protect – in just a few minutes! No matter what stage of data governance you are, ALTR gives you the space and tools to grow at your own pace.
Going to the gym can be tough to keep up. At the end of a long day or before you even get going, you have to find the motivation to put your gear on, drive to the gym no matter the weather or the traffic, then you have to actually do the work! And you have to do it 3 to 5 times a week to make an impact.
With ALTR, once you set it up, you can just sit back and let it do the work for you. ALTR automates access to data, limits data consumption based on the rules you set, and blocks unauthorized access automatically. Our data usage heatmaps show your top users, what data they accessed, when and how much. It’s like a Fitbit for your data consumption. The difference is you don’t have to do a thing to see the numbers go up. ALTR helps you build up your core data governance, control, protect muscles so you can focus on the heavy lifting of moving sensitive data to the cloud.
We built the ALTR Free plan to give everyone access to effective data control and protection – we’ve done away with long implementations, high costs, complicated contracts, time-consuming maintenance. We’ve eliminated all the roadblocks, and there are no more excuses.
The ALTR Free plan can help you kick start your data control and protection fitness in 2022. And it’s safer than a Peloton.


Today’s data-driven enterprises know that making data available across the company can lead to improved results—from higher sales to better customer satisfaction to improved market share. But the business-level need to make data available has been in conflict with the business-level requirement that data be shared securely. These competing business drivers have led to an odd mismatch between what companies would like to do with data and what they have actually been able to achieve. In order to provide data both swiftly and securely to users, companies should focus on these 3 keys to faster and safer data delivery.
Before you can provide data to users, you must document what data you have. This means discovering data across databases and software, in cloud SaaS platforms and on-premises in legacy databases. The data must be typed: are they names, social security numbers or email addresses? Then it should be tagged by business context: is the email address from Salesforce or HR? Is it a prospect or employee?
Once the data has been discovered, analyzed and classified, the available data types and tags can be displayed to users via a data catalog—just like any e-commerce platform. Users should be able to search for data to enable a specific use case, such as sharing custom coupons near specific locations. They can select email addresses, GPS data, available inventory and any other information needed to achieve the goal and add those to their “data shopping cart”, regardless of where the data is from or located. The backend structure is completely seamless to users. The goal is to make it as easy as ordering from Amazon.

Unfortunately, here’s where the e-commerce metaphor falls apart. While the e-commerce process is mostly automated all the way through, security-focused “default to no” and Zero Trust policies have forced companies to evaluate requests individually and manually as they come in. This leads to labor-intensive data control and release processes on the back end. Once a user “places an order” for data, that sets off a workflow that primarily consists of email notifications to one or more data stewards. What should be a 5-minute fulfillment task can actually take 3-4 days. Data stewards must check the policies to confirm whether the user is authorized to have access to the data. The requester may have asked for data from multiple locations with various owners – Snowflake data may be owned by analytics and Oracle on-prem data by IT or operations. There can often be different data stewards for different data sets, and review/approval tasks often fall on data teams who have other full-time responsibilities on top of their data steward duties.
Such a manual process is rife with human error. Data stewards could accidentally provide access that is too broad or for too long or just to the wrong data. Because human error can lead to data breaches, manual processes increase the risk of that. Still, this process was almost manageable when the requests were 1 or 2 per week. But customers are telling us that they’re seeing 1 or 2 per hour now. It’s simply not sustainable.

Unifying and automating the entire process solves this issue and upgrades the complete data delivery experience. It makes the whole mechanism faster and more secure than the sum of its parts. The data governance tool acts as the brain, knowing who should have access to which data. Automated data discovery, analysis and cataloging with SaaS-based tools like OneTrust and Collibra allow companies to find data across the entire ecosystem, document data lineage, and type and tag it. Once that data has been identified, policy and permissions can be applied.
Then the access control tool like ALTR acts as the muscle, regulating access based on commands it receives from the brain, bypassing the time-consuming and error-prone manual authorization workflow. ALTR’s SaaS-based solution also spans across multiple database types – both on prem and in the cloud – to update access permissions in real time. This provides one central command and control center across the data ecosystem, unlike proxy-based solutions that must be implemented and managed separately for each database. And ALTR also helps define and control what “access” means – is it root level access or a reader account? Is the data masked or limited by amount? For example, HIPAA regulations require that only the minimum necessary standard of data is available to the user to achieve their task.

Finally, the constant consumption feedback ALTR provides acts as the senses, letting the brain know what data is actually being consumed, by whom. This allows teams to double check usage against existing policies and correct any misalignments. If we go back to the Amazon example, this would be as if someone bought too many masks to resell during a pandemic, and Amazon stopped the purchase as against its policies.
When users have access to the data they need in minutes instead of days, the whole company can perform better. When unification and automation not only deliver that speed, but also reduce the risk of human error leading to a breach, the company’s entire data set is safer even as its being shared. Now the promise of data usage across the company can be delivered.

We’re continuing our series of predictions for the 2022 data governance landscape from ALTR leaders Dave Sikora, James Beecham, Doug Wick, and Pete Martin.
All the activity around data, especially sensitive data, we discussed in our previous predictions (1, 2 and 3) will continue to draw attention from regulators. We have already seen several state-level laws including CCPA and CPRA in 2020 in California, Virginia and Colorado passed this year, and active bills in at least 6 other states. Every time a new state law is passed it increases the complexity of data access controls for governance and security teams.
And this will make data literacy just as necessary as financial literacy for executives, including board members. They’ll need to have a crisp understanding of how data works in the business, where it comes from, who it goes to, what data is meaningful and what can be ignored. Leaders will need to understand what’s required by regulations and how the way company is using data creates regulatory risk. We expect that soon company executives will be looking at “data flow” statements alongside cash flow statements each quarter.
Companies that have this competency baked into their business will be in a better position to weather the next big regulatory storm: a U.S. federal data privacy law on the level of the Sarbanes-Oxley Act of 2002. “SOX”, passed in reaction to several financial scandals including Enron, Tyco and WorldCom, requires corporate officers of publicly traded companies to personally certify that the company's financial statements are accurate. Officers who sign statements they know are inaccurate can face criminal charges and penalties including prison. We certainly hope that we don’t see scandals as shocking as those of the early 2000s, but if data breaches continue to worsen, we can expect legislation that requires publicly traded companies to have board-level data audit committees documenting how the company is protecting sensitive data, with CEOs and CDOs required to sign accountability statements.
To see all our predictions for 2022, download our white paper here.


We’re continuing our series of predictions for the 2022 data governance landscape from ALTR leaders Dave Sikora, James Beecham, Doug Wick, and Pete Martin.
In our last post, we talked about how the democratization of data access will lead to an order of magnitude increase in the credentialed access threat. But a positive effect of the growing democratization of data is the opportunity for companies to truly become “data-driven,” unlocking enormous economic value over the next five to 10 years. Currently, companies don’t really have a good handle of what’s truly going on inside their business – broadly across the various functions or in detail down to the transaction level. They don’t have the visibility or measurement around operations or their customers. But by making the data available to everybody, companies will get more operationally efficient across the board: marketing will get more effective at reaching potential customers, logistics will get more proficient at moving supplies and products through the business, and so on.
At the same time data is spreading across the business, its importance is pushing the prominence of data up the executive ladder. This will lead to the elevation of the Chief Data Officer. Their responsibility will be to use all this data to make sense of the business – to correlate data points and create a high-level understanding of how the company is operating from a data flow perspective. We’re already seeing this happening to a certain extent with the percentage of organizations reporting the appointment of a CDO increasing from 12% in 2012 to 65% in 2021. This will have the side effect of pushing the CIO and the Information Technology teams lower in ranking, potentially reporting to the CDO, simply focused on putting the technology structure in place to enable a data-driven strategy.
Venture Beat calls the combination of data and AI embedded within companies for analytical and operational purposes “the beginning of the era of the intelligent, automated enterprise.”
Obviously, we’re just at the very early stages of this massive upheaval, but even what we’ve seen so far will help support what Gartner notes are CEO priorities for 2022: growth, digitalization and efficiency. These are all enabled if you can make better sense of your data. With disparate applications and disparate data points, the only way to take the business to the next level is to connect all those dots to create a holistic picture and uncover real insight.
Watch our blog for more predictions to come around new risks to data, the crucial role of data in the business, and the regulatory environment ahead…


Heading into the holidays, we can’t help but look back at the whirlwind last two years. The COVID-19 pandemic caused a disruption unlike any we’ve seen in the last few decades. Employees across the world began working remotely like never before. Because data has become such a critical part of this work, it needed to follow the employees, quickly escalating digital transformation and the move of data to the Cloud. Snowflake’s record setting IPO in September 2020 demonstrates the value of this opportunity. But the shift also put an abrupt burden on IT teams to protect that remote work and the data required from new threats and escalating old ones. Data thieves and hackers took advantage of the disruption to step up attacks, like the recent Robinhood leak that exposed data of 7 million customers. As data exfiltration and PII leaks continued, regulatory attention around protecting personal information in the US increased.
All in all, it’s a challenging yet thrilling time to be part of the data ecosystem. And data governance and security are more critical than ever.
As we look toward 2022, it’s a given that data will continue moving to and consolidating in the Cloud. But this will lead to other shifts in the data governance landscape, uncovering surprising new possibilities and challenges for companies who want to stay ahead of the competition by making the most of their data. Over the next few weeks, we’ll share some predictions from ALTR leaders Dave Sikora, James Beecham, Doug Wick, and Pete Martin to help companies know what they might expect in 2022.
Centralizing data in the cloud enables increased flexibility, availability and sharing of data – within the enterprise and without. In the past, if you wanted to share data that lived in an on-prem datacenter with another group or with an external partner, you would have to extract and then email or FTP the file – a cumbersome, manual process. Increasingly, companies will take steps to make data more easily available via the cloud – to connect applications, to monetize it or even utilize it to create a more effective AI.
For example, earlier this year, NBC Universal announced a new solution to monetize the audience data it gathers by making it available to partners, on a cross-cloud data clean room environment powered by Snowflake. Advertisers will be able to safely and securely join their own data, without exposing any viewer personally identifiable information (PII). The Snowflake platform lets NBC Universal govern what data is housed in the clean room, how data can be joined, what types of analyses can be performed on the data, and what data can leave. Disney is doing something similar by making Snowflake its single source of data to share securely with its internal teams and partners. Snowflake is enabling the monetization of sharing further with their Data Marketplace which allows companies to offer up unique, proprietary data to Snowflake customers to utilize along with their own data.
Secure cloud-based sharing will also help overcome one of the main ML/AI roadblocks: training data. 91.9% of firms report that the pace of investment in Big Data and AI projects is accelerating, but AIs don’t come fully formed out the box – they require massive amounts of data to learn on to be effective. Companies may contract with an ML or AI provider, but the model needs to be trained on relevant data for that specific company’s use case before deployment. Data privacy concerns have limited the ability to provide real data to AI vendors, with companies in some cases relying on synthetic data, but implementing secure data sharing allows for use of real data instead.
Essentially, the ability to securely share sensitive data easily from the cloud will enable increased data sharing and increased insights.
Watch our blog for more predictions to come around new risks to data, the crucial role of data in the business, and the regulatory environment ahead…


We’re continuing our series of predictions for the 2022 data governance landscape from ALTR leaders Dave Sikora, James Beecham, Doug Wick, and Pete Martin.
In our first post, we talked about how companies will utilize secure data sharing to get more value out of data. Next year, we’re all confident that data will become even more critical to business and will continue consolidating in the Cloud. But this consolidated data pool will have the unfortunate side effect of drawing criminal attention. Data that used to exist in specific, disparate software or databases such as Workday, Salesforce or SAP is being uploaded into a consolidated cloud database, accessible from all over the world, with a single username and log in supplying entry. As this trend continues, these cloud data platforms will become an even more attractive target for “hackers.”
But can it even be called “hacking” when companies leave the door open? Many of the most well-known data breaches of the last few years were the result of misconfigured cloud database or application security. A June 2021 IDC survey of CISOs and security decision makers showed that almost 100% of companies had experienced a cloud data breach in the past 18 months.
While data warehousing has been growing for the last ten to twenty years, at the beginning, only a small group of individuals had access to the data. As the realization of the possibilities this information provides has spread across the business, there has been an increased push to democratize access. Companies have started handing out access to data like Oprah handed out car keys – “You get credentials, and you get credentials, and you get credentials!” This, along with the growth in data sharing, increases the credentialed access threat potentially by an order of magnitude. And that unfortunately means, for the sixth year in a row, we will likely see “credentialed access” as one of the top drivers for data breaches in the 2022 Verizon Data Breach Investigation Report and the IBM Cost of a Data Breach Report.
Watch our blog for more predictions to come around new risks to data, the crucial role of data in the business, and the regulatory environment ahead…


In 2020, you moved your simple and easy workloads into a Cloud Data Platform like Snowflake but got stuck moving more sensitive data workloads for security, privacy, or compliance reasons. In this post, you’ll learn how easy it has become to pair your Cloud Data Platform with a fully SaaS delivered and credentialed security provider to overcome the challenges of using sensitive data in the cloud. Whether you're the data engineer, the data architect tasked to use the data, or the security engineer tasked with securing the data, pairing ALTR with Snowflake will help quickly turn a data workload ‘no’ into a workload ‘yes’!
We all remember our first time logging into that beautiful blue Snowflake web UI, running our first sample query on the sample data set, and how cool it felt. But we quickly got our snow boots under us and wanted to start using real data. At first, migration was easy. Let's pretend you're on the marketing analytics team and wanted to cross-reference your marketing spend in AdWords with this month's orders broken down by zip code — with a few clicks, you have easily added AdWords data into Snowflake as well as data from your eCommerce SaaS provider. You can now easily run reports either from the last 30 days or the last three years, and you didn't have to call IT. The rush of being in control of your marketing analytics destiny is pretty neat, so you begin to add other sources into Snowflake, removing data silos, and making your job easier and faster. This goes on for a few months, and everything is dandy.
Then you get the great idea of importing your customers' information from Salesforce Marketing Cloud emails and campaigns. You want this data to cross-reference web cookies or email responses to coupons you've been using. You'd also love to get some of the more sensitive data that still lives on-prem in a legacy operational database. Only this time when you go to quickly import this data, you are blocked first by the firewall — you don't have a username/password and you realize the security teams can see you trying to access that information, then you get a call from your local neighborhood DBA and security engineer. You explain what you were trying to do and show them all the cool stuff you've been doing with Snowflake and how much better the company will for the work. But they point out that you cannot just simply move this customer data as you did with the other data. It's at this moment that you realize you're standing on the edge of a cliff. This cliff looks dangerous and leads to a canyon that is vast and full of wild GDPR and CCPA animals as well as the worn-out brands that have had massive data breaches. The canyon is real and it causes everyone on that call, DBA, security, and you to stop in your tracks.
But on the other side of the canyon, you see increased revenues, reduced marketing waste, and more efficient campaigns. All things the business would love to have and use. So you begin to brainstorm with the security and DBA teams. “What if we just did this...?”, or “How about we try to port legacy security system X to Snowflake?” “Won't work,” says the DBA and security teams – running VPN connections between on-prem and Snowflake isn't possible; or the latency impact it will have makes using Snowflake not possible; or the privileged access management tool (PAM) you have doesn't support Snowflake and will never support Snowflake.
Everyone is on the same page trying to get across that canyon together but it seems hard to navigate the dangers of the canyon. You need a bridge. Something stable and safe you can walk on to cross the canyon and bring that customer data with you. It needs to be flexible enough to handle different types of data because if you can get the customer data you want across the canyon, then others will surely try to bring more sensitive data with them behind you. It needs to be strong enough to stand up to the dangers of the wild compliance and regulations animals below it all howling for your hard-earned revenue if you screw up. It almost feels like you can't make it across.
One day you wake up and see a post on LinkedIn from some guy who is a 2nd connection to the person you shared a cube with as an intern 6 years ago. He's talking about data security being delivered as SaaS, or DSaaS (Data Security as a Service), and how it has a native integration with Snowflake to help observe data access and detect and respond to improper access — they even offer tokenization of data at rest. All of this can be enabled quickly with Snowflake? They have attestations and certifications to store and control access to PCI, PII, and HIPAA data types. You reconvene the DBA and security engineering team, standing on the edge of the canyon once more, you spec out what could be a pretty nice bridge to get you across. This bridge is ALTR DSaaS. Everyone agrees after researching the product and trialing the software that this could be the answer.
From the trial, everyone learned that they could:
Low and behold, everyone’s boss signs off on the usage since ALTR DSaaS has the features and scalability needed to cross the canyon safely. You can now begin to move sensitive workloads without fear that someone will be able to steal credentials and take data. You know after running the trial that SQL injection attacks won't work with ALTR in place. You can provide all needed parties with Observability reports that policy is in place and is being enforced. ALTR DSaaS has satisfied even the most stringent of requirements because it extends beyond RBAC controls and places policy on data, ensuring that only authorized users access data, and only as much data as is allowed. Information at rest can be protected without the overhead of encryption keys, and the SaaS deployment matches Snowflake scale so the data is actually usable even with the highest levels of security.
Canyon crossed, goals achieved, next workload please.
To learn more about how ALTR can protect your sensitive data in the cloud, check out this white paper.