Format-Preserving Encryption: A Deep Dive into FF3-1 Encryption Algorithm




In the ever-evolving landscape of data security, protecting sensitive information while maintaining its usability is crucial. ALTR’s Format Preserving Encryption (FPE) is an industry disrupting solution designed to address this need. FPE ensures that encrypted data retains the same format as the original plaintext, which is vital for maintaining compatibility with existing systems and applications. This post explores ALTR's FPE, the technical details of the FF3-1 encryption algorithm, and the benefits and challenges associated with using padding in FPE.
Format Preserving Encryption is a cryptographic technique that encrypts data while preserving its original format. This means that if the plaintext data is a 16-digit credit card number, the ciphertext will also be a 16-digit number. This property is essential for systems where data format consistency is critical, such as databases, legacy applications, and regulatory compliance scenarios.
The FF3-1 encryption algorithm is a format-preserving encryption method that follows the guidelines established by the National Institute of Standards and Technology (NIST). It is part of the NIST Special Publication 800-38G and is a variant of the Feistel network, which is widely used in various cryptographic applications. Here’s a technical breakdown of how FF3-1 works:
1. Feistel Network: FF3-1 is based on a Feistel network, a symmetric structure used in many block cipher designs. A Feistel network divides the plaintext into two halves and processes them through multiple rounds of encryption, using a subkey derived from the main key in each round.
2. Rounds: FF3-1 typically uses 8 rounds of encryption, where each round applies a round function to one half of the data and then combines it with the other half using an XOR operation. This process is repeated, alternating between the halves.
3. Key Scheduling: FF3-1 uses a key scheduling algorithm to generate a series of subkeys from the main encryption key. These subkeys are used in each round of the Feistel network to ensure security.
4. Tweakable Block Cipher: FF3-1 includes a tweakable block cipher mechanism, where a tweak (an additional input parameter) is used along with the key to add an extra layer of security. This makes it resistant to certain types of cryptographic attacks.
5. Format Preservation: The algorithm ensures that the ciphertext retains the same format as the plaintext. For example, if the input is a numeric string like a phone number, the output will also be a numeric string of the same length, also appearing like a phone number.
1. Initialization: The plaintext is divided into two halves, and an initial tweak is applied. The tweak is often derived from additional data, such as the position of the data within a larger dataset, to ensure uniqueness.
2. Round Function: In each round, the round function takes one half of the data and a subkey as inputs. The round function typically includes modular addition, bitwise operations, and table lookups to produce a pseudorandom output.
3. Combining Halves: The output of the round function is XORed with the other half of the data. The halves are then swapped, and the process repeats for the specified number of rounds.
4. Finalization: After the final round, the halves are recombined to form the final ciphertext, which maintains the same format as the original plaintext.
Implementing FPE provides numerous benefits to organizations:
1. Compatibility with Existing Systems: Since FPE maintains the original data format, it can be integrated into existing systems without requiring significant changes. This reduces the risk of errors and system disruptions.
2. Improved Performance: FPE algorithms like FF3-1 are designed to be efficient, ensuring minimal impact on system performance. This is crucial for applications where speed and responsiveness are critical.
3. Simplified Data Migration: FPE allows for the secure migration of data between systems while preserving its format, simplifying the process and ensuring compatibility and functionality.
4. Enhanced Data Security: By encrypting sensitive data, FPE protects it from unauthorized access, reducing the risk of data breaches and ensuring compliance with data protection regulations.
5. Creation of production-like data for lower trust environments: Using a product like ALTR’s FPE, data engineers can use the cipher-text of production data to create useful mock datasets for consumption by developers in lower-trust development and test environments.
Padding is a technique used in encryption to ensure that the plaintext data meets the required minimum length for the encryption algorithm. While padding is beneficial in maintaining data structure, it presents both advantages and challenges in the context of FPE:
1. Consistency in Data Length: Padding ensures that the data conforms to the required minimum length, which is necessary for the encryption algorithm to function correctly.
2. Preservation of Data Format: Padding helps maintain the original data format, which is crucial for systems that rely on specific data structures.
3. Enhanced Security: By adding extra data, padding can make it more difficult for attackers to infer information about the original data from the ciphertext.
1. Increased Complexity: The use of padding adds complexity to the encryption and decryption processes, which can increase the risk of implementation errors.
2. Potential Information Leakage: If not implemented correctly, padding schemes can potentially leak information about the original data, compromising security.
3. Handling of Padding in Decryption: Ensuring that the padding is correctly handled during decryption is crucial to avoid errors and data corruption.
ALTR's Format Preserving Encryption, powered by the technically robust FF3-1 algorithm and married with legendary ALTR policy, offers a comprehensive solution for encrypting sensitive data while maintaining its usability and format. This approach ensures compatibility with existing systems, enhances data security, and supports regulatory compliance. However, the use of padding in FPE, while beneficial in preserving data structure, introduces additional complexity and potential security challenges that must be carefully managed. By leveraging ALTR’s FPE, organizations can effectively protect their sensitive data without sacrificing functionality or performance.
For more information about ALTR’s Format Preserving Encryption and other data security solutions, visit the ALTR documentation
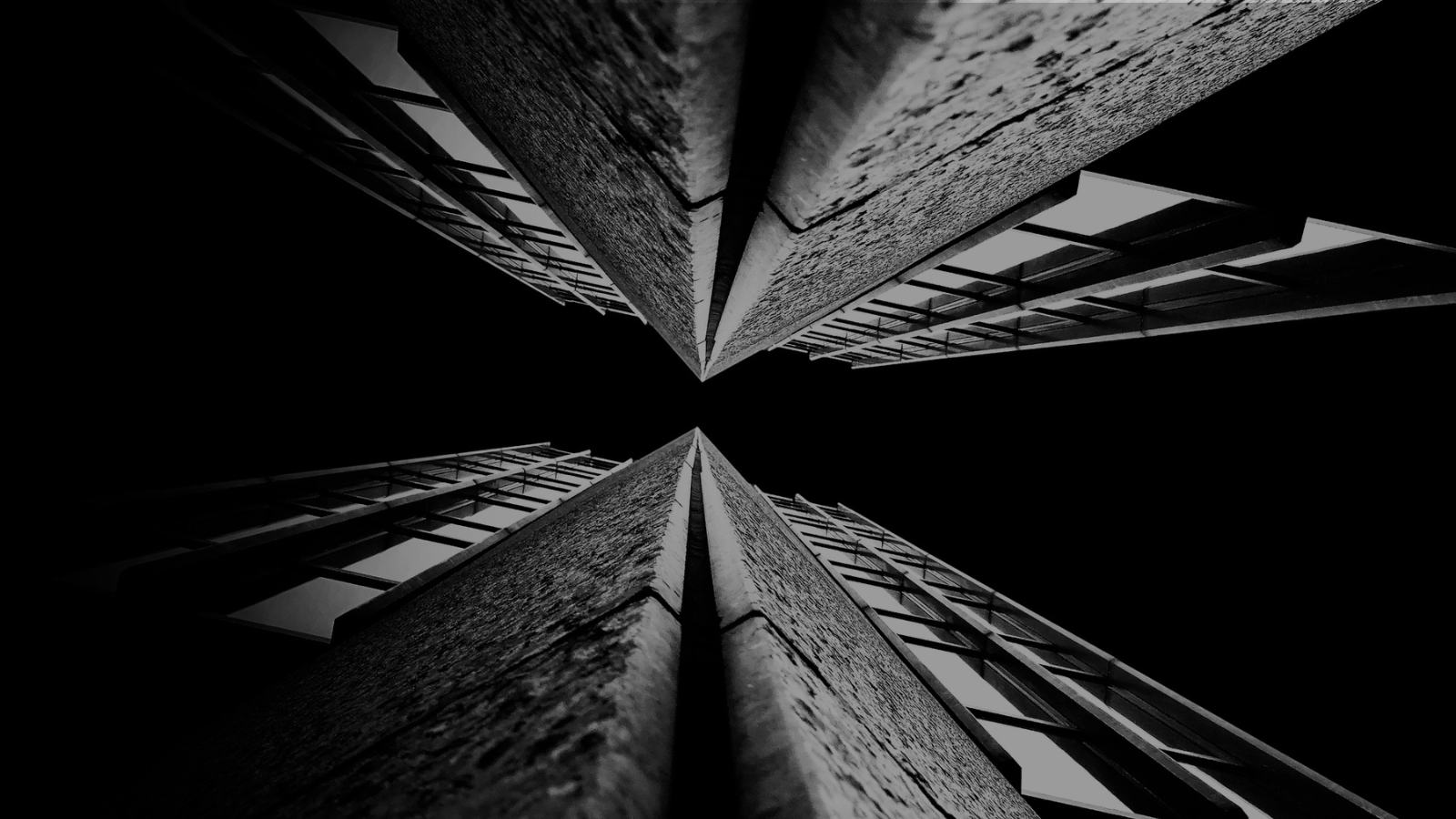
For years (even decades) sensitive information has lived in transactional and analytical databases in the data center. Firewalls, VPNs, Database Activity Monitors, Encryption solutions, Access Control solutions, Privileged Access Management and Data Loss Prevention tools were all purchased and assembled to sit in front of, and around, the databases housing this sensitive information.
Even with all of the above solutions in place, CISO’s and security teams were still a nervous wreck. The goal of delivering data to the business was met, but that does not mean the teams were happy with their solutions. But we got by.
The advent of Big Data and now Generative AI are causing businesses to come to terms with the limitations of these on-prem analytical data stores. It’s hard to scale these systems when the compute and storage are tightly coupled. Sharing data with trusted parties outside the walls of the data center securely is clunky at best, downright dangerous in most cases. And forget running your own GenAI models in your datacenter unless you can outbid Larry, Sam, Satya, and Elon at the Nvidia store. These limits have brought on the era of cloud data platforms. These cloud platforms address the business needs and operational challenges, but they also present whole new security and compliance challenges.
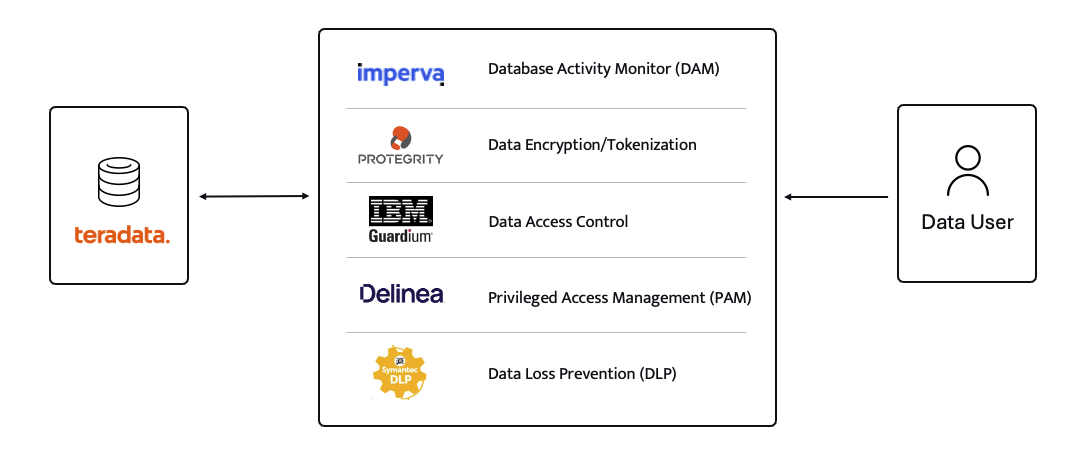
ALTR’s platform has been purpose-built to recreate and enhance these protections required to use Teradata for Snowflake. Our cutting-edge SaaS architecture is revolutionizing data migrations from Teradata to Snowflake, making it seamless for organizations of all sizes, across industries, to unlock the full potential of their data.
What spurred this blog is that a company reached out to ALTR to help them with data security on Snowflake. Cool! A member of the Data & Analytics team who tried our product and found love at first sight. The features were exactly what was needed to control access to sensitive data. Our Format-Preserving Encryption sets the standard for securing data at rest, offering unmatched protection with pricing that's accessible for businesses of any size. Win-win, which is the way it should be.
Our team collaborated closely with this person on use cases, identifying time and cost savings, and mapping out a plan to prove the solution’s value to their organization. Typically, we engage with the CISO at this stage, and those conversations are highly successful. However, this was not the case this time. The CISO did not want to meet with our team and practically stalled our progress.
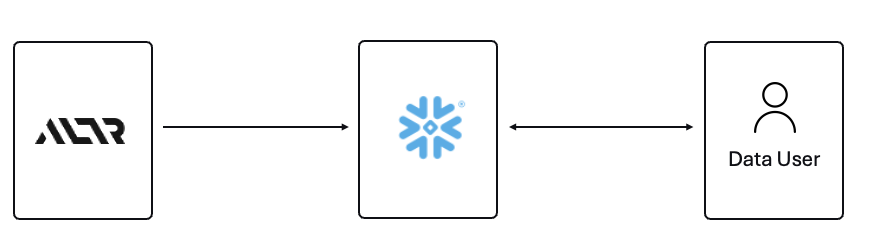
The CISO’s point of view was that ALTR’s security solution could be completely disabled, removed, and would not be helpful in the case of a compromised ACCOUNTADMIN account in Snowflake. I agree with the CISO, all of those things are possible. Here is what I wanted to say to the CISO if they had given me the chance to meet with them!
The ACCOUNTADMIN role has a very simple definition, yet powerful and long-reaching implications of its use:
One of the main points I would have liked to make to the CISO is that as a user of Snowflake, their responsibility to secure that ACCOUNTADMIN role is squarely in their court. By now I’m sure you have all seen the news and responses to the Snowflake compromised accounts that happened earlier this year. It is proven that unsecured accounts by Snowflake customers caused the data theft. There have been dozens of articles and recommendations on how to secure your accounts with Snowflake and even a mandate of minimum authentication standards going forward for Snowflake accounts. You can read more information here, around securing the ACCOUNTADMIN role in Snowflake.
I felt the CISO was missing the point of the ALTR solution, and I wanted the chance to explain my perspective.
ALTR is not meant to secure the ACCOUNTADMIN account in Snowflake. That’s not where the real risk lies when using Snowflake (and yes, I know—“tell that to Ticketmaster.” Well, I did. Check out my write-up on how ALTR could have mitigated or even reduced the data theft, even with compromised accounts). The risk to data in Snowflake comes from all the OTHER accounts that are created and given access to data.
The ACCOUNTADMIN role is limited to one or two people in an organization. These are trusted folks who are smart and don’t want to get in trouble (99% of the time). On the other hand, you will have potentially thousands of non-ACCOUNTADMIN users accessing data, sharing data, screensharing dashboards, re-using passwords, etc. This is the purpose of ALTR’s Data Security Platform, to help you get a handle on part of the problem which is so large it can cause companies to abandon the benefits of Snowflake entirely.
There are three major issues outside of the ACCOUNTADMIN role that companies have to address when using Snowflake:
1. You must understand where your sensitive is inside of Snowflake. Data changes rapidly. You must keep up.
2. You must be able to prove to the business that you have a least privileged access mechanism. Data is accessed only when there is a valid business purpose.
3. You must be able to protect data at rest and in motion within Snowflake. This means cell level encryption using a BYOK approach, near-real-time data activity monitoring, and data theft prevention in the form of DLP.
The three issues mentioned above are incredibly difficult for 95% of businesses to solve, largely due to the sheer scale and complexity of these challenges. Terabytes of data and growing daily, more users with more applications, trusted third parties who want to collaborate with your data. All of this leads to an unmanageable set of internal processes that slow down the business and provide risk.
ALTR’s easy-to-use solution allows Virgin Pulse Data, Reporting, and Analytics teams to automatically apply data masking to thousands of tagged columns across multiple Snowflake databases. We’re able to store PII/PHI data securely and privately with a complete audit trail. Our internal users gain insight from this masked data and change lives for good.
- Andrew Bartley, Director of Data Governance
I believed the CISO at this company was either too focused on the ACCOUNTADMIN problem to understand their other risks, or felt he had control over the other non-admin accounts. In either case I would have liked to learn more!
There was a reason someone from the Data & Analytics team sought out a product like ALTR. Data teams are afraid of screwing up. People are scared to store and use sensitive data in Snowflake. That is what ALTR solves for, not the task of ACCOUNTADMIN security. I wanted to be able to walk the CISO through the risks and how others have solved for them using ALTR.
The tools that Snowflake provides to secure and lock down the ACCOUNTADMIN role are robust and simple to use. Ensure network policies are in place. Ensure MFA is enabled. Ensure you have logging of ACCOUNTADMIN activity to watch all access.
I wish I could have been on the conversation with the CISO to ask a simple question, “If I show you how to control the ACCOUNTADMIN role on your own, would that change your tone on your teams use of ALTR?” I don’t know the answer they would have given, but I know the answer most CISO’s would give.
Nothing will ever be 100% secure and I am by no means saying ALTR can protect your Snowflake data 100% by using our platform. Data security is all about reducing risk. Control the things you can, monitor closely and respond to the things you cannot control. That is what ALTR provides day in and day out to our customers. You can control your ACCOUNTADMIN on your own. Let us control and monitor the things you cannot do on your own.

Since 2015 the migration of corporate data to the cloud has rapidly accelerated. At the time it was estimated that 30% of the corporate data was in the cloud compared to 2022 where it doubled to 60% in a mere seven years. Here we are in 2024, and this trend has not slowed down.
Over time, as more and more data has moved to the cloud, new challenges have presented themselves to organizations. New vendor onboarding, spend analysis, and new units of measure for billing. This brought on different cloud computer-related cost structures and new skillsets with new job titles. Vendor lock-in, skill gaps, performance and latency and data governance all became more intricate paired with the move to the cloud. Both operational and transactional data were in scope to reap the benefits promised by cloud computing, organizational cost savings, data analytics and, of course, AI.
The most critical of these new challenges revolve around a focus on Data Security and Privacy. The migration of on-premises data workloads to the Cloud Data Warehouses included sensitive, confidential, and personal information. Corporations like Microsoft, Google, Meta, Apple, Amazon were capturing every movement, purchase, keystroke, conversation and what feels like thought we ever made. These same cloud service providers made this easier for their enterprise customers to do the same. Along came Big Data and the need for it to be cataloged, analyzed, and used with the promise of making our personal lives better for a cost. The world's population readily sacrificed privacy for convenience.
The moral and ethical conversation would then begin, and world governments responded with regulations such as GDPR, CCPA and now most recently the European Union’s AI Act. The risk and fines have been in the billions. This is a story we already know well. Thus, Data Security and Privacy have become a critical function primarily for the obvious use case, compliance, and regulation. Yet only 11% of organizations have encrypted over 80% of their sensitive data.
With new challenges also came new capabilities and business opportunities. Real time analytics across distributed data sources (IoT, social media, transactional systems) enabling real time supply chain visibility, dynamic changes to pricing strategies, and enabling organizations to launch products to market faster than ever. On premise applications could not handle the volume of data that exists in today’s economy.
Data sharing between partners and customers became a strategic capability. Without having to copy or move data, organizations were enabled to build data monetization strategies leading to new business models. Now building and training Machine Learning models on demand is faster and easier than ever before.
To reap the benefits of the new data world, while remaining compliant, effective organizations have been prioritizing Data Security as a business enabler. Format Preserving Encryption (FPE) has become an accepted encryption option to enforce security and privacy policies. It is increasingly popular as it can address many of the challenges of the cloud while enabling new business capabilities. Let’s look at a few examples now:
Real Time Analytics - Because FPE is an encryption method that returns data in the original format, the data remains useful in the same length, structure, so that more data engineers, scientists and analysts can work with the data without being exposed to sensitive information.
Data Sharing – FPE enables data sharing of sensitive information both personal and confidential, enabling secure information, collaboration, and innovation alike.
Proactive Data Security– FPE allows for the anonymization of sensitive information, proactively protecting against data breaches and bad actors. Good holding to ransom a company that takes a more proactive approach using FPE and other Data Security Platform features in combination.
Empowered Data Engineering – with FPE data engineers can still build, test and deploy data transformations as user defined functions and logic in stored procedures or complied code will run without failure. Data validations and data quality checks for formats, lengths and more can be written and tested without exposing sensitive information. Federated, aggregation and range queries can still run without fail without the need for decryption. Dynamic ABAC and RBAC controls can be combined to decrypt at runtime for users with proper rights to see the original values of data.
Cost Management – While FPE does not come close to solving Cost Management in its entirety, it can definitely contribute. We are seeing a need for FPE as an option instead of replicating data in the cloud to development, test, and production support environments. With data transfer, storage and compute costs, moving data across regions and environments can be really expensive. With FPE, data can be encrypted and decrypted with compute that is a less expensive option than organizations' current antiquated data replication jobs. Thus, making FPE a viable cost savings option for producing production ready data in non-production environments. Look for a future blog on this topic and all the benefits that come along.
FPE is not a silver bullet for protecting sensitive information or enabled these business use cases. There are well documented challenges in the FF1 and FF3-1 algorithms (another blog on that to come). A blend of features including data discovery, dynamic data masking, tokenization, role and attribute-based access controls and data activity monitoring will be needed to have a proactive approach towards security within your modern data stack. This is why Gartner considers a Data Security Platform, like ALTR, to be one of the most advanced and proactive solutions for Data security leaders in your industry.
Securing sensitive information is now more critical than ever for all types of organizations as there have been many high-profile data breaches recently. There are several ways to secure the data including restricting access, masking, encrypting or tokenization. These can pose some challenges when using the data downstream. This is where Format Preserving Encryption (FPE) helps.
This blog will cover what Format Preserving Encryption is, how it works and where it is useful.
Whereas traditional encryption methods generate ciphertext that doesn't look like the original data, Format Preserving Encryption (FPE) encrypts data whilst maintaining the original data format. Changing the format can be an issue for systems or humans that expect data in a specific format. Let's look at an example of encrypting a 16-digit credit card number:
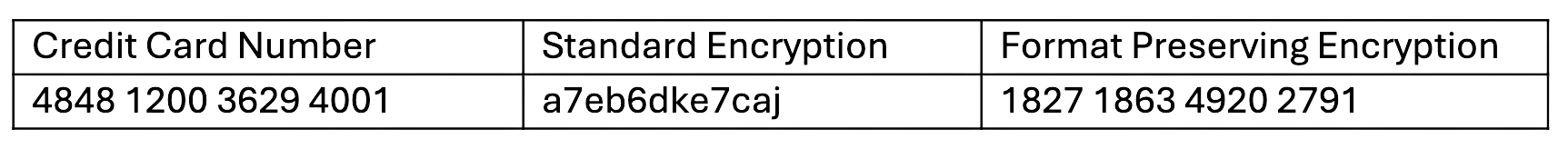
As you can see with a Standard Encryption type the result is a completely different output. This may result in it being incompatible with systems which require or expect a 16-digit numerical format. Using FPE the encrypted data still looks like a valid 16-digit number. This is extremely useful for where data must stay in a specific format for compatibility, compliance, or usability reasons.
Format Preserving Encryption in ALTR works by first analyzing the column to understand the input format and length. Next the NIST algorithm is applied to encrypt the data with the given key and tweak. ALTR applies regular key rotation to maximize security. We also support customers bringing their own keys (BYOK). Data can then selectively be decrypted using ALTR’s access policies.
FPE offers several benefits for organizations that deal with structured data:
1. Adds extra layer of protection: Even if a system or database is breached the encryption makes sensitive data harder to access.
2. Original Data Format Maintained: FPE preserves the original data structure. This is critical when the data format cannot be changed due to system limitations or compliance regulations.
3. Improves Usability: Encrypted data in an expected format is easier to use, display and transform.
4. Simplifies Compliance: Many regulations like PCI-DSS, HIPAA, and GDPR will mandate safeguarding, such as encryption, of sensitive data. FPE allows you to apply encryption without disrupting data flows or reporting, all while still meeting regulatory requirements.
FPE is widely adopted in industries that regularly handle sensitive data. Here are a few common use cases:
ALTR offers various masking, tokenization and encryption options to keep all your Snowflake data secure. Our customers are seeing the benefit of Format Preserving Encryption to enhance their data protection efforts while maintaining operational efficiency and compliance. For more information, schedule a product tour or visit the Snowflake Marketplace.

We are proud to announce that ALTR has been selected as a finalist for Bank Director’s Best of FinXTech Awards, in the category “Best Solution for Protecting a Bank.” This selection recognizes the power of our data security as a service (DSaaS) platform to protect the sensitive data created, stored, and shared by financial software applications.
Our DSaaS approach to safeguard data embeds governance and at-rest protection natively into applications. That allows application teams to implement security during the development cycle and then hand off the management of governance and protection policies to security and compliance teams, rather than having security added as an afterthought by IT departments. This approach results in better protection from breaches and intrusion for application data.
ALTR DSaaS has been adopted by companies in diverse industries. The FinXTech selection particularly cited our work with Q2 eBanking, a multi-billion dollar digital banking solutions company that selected the ALTR platform to create Q2 TrustView. ALTR renders the data used by Q2 TrustView virtually inaccessible to bad actors, providing the highest level of protection for the account holders at the financial institutions that Q2 serves.
Through the Best of FinXTech Awards, Bank Director recognizes the efforts of emerging financial technology solutions that best help a financial institution grow revenues, create efficiencies, or reduce risk. Bank Director, a leading information resource for banking leaders, awards its Best of FinXTech to top-rated financial technology companies in seven different categories. Awards are based on Bank Director’s analysis of each solution’s capabilities, which includes phone interviews with each of the finalists and their banking clients, in-depth case studies on each solution, and the votes of a panel of industry experts.
Mika Moser, President of Bank Director and FinXTech, offered more perspective on ALTR’s selection: “As a trusted resource for U.S. Banks, Bank Director are excited to recognize technology companies, like ALTR, who are driving real growth for financial institutions through new products, increased security, and operational enhancements.”
By delivering DSaaS, ALTR allows developers to embed data monitoring, governance, and at-rest protection natively at the application layer. Supported by private blockchain technology, our platform provides an API and scalable smart database drivers that make it possible to virtually eliminate data access risks, making applications more portable and cost efficient to implement and maintain than traditional applianceware or outdated endpoint security systems.
We are pleased that Bank Director, which connects U.S. bank leaders with technology partners driving innovation, has recognized us with this selection.

When Tableau was founded in 2003, business intelligence (BI) was still in its infancy. It was a critical but specialized skillset utilized by a handful of power users in a company who ran reports and pulled visualizations for the rest of the company. When the quantity of users was small it was doable to install the Tableau desktop client on that limited number of systems, and the relatively small number of users made tracking every user’s access to data feasible.
Since then, the amount of data business creates, stores and utilizes has exploded, along with the value extracted in analysis of that data. Whether it was the insights gained by using a BI tool or just the dazzle of gorgeous charts and dashboards, business professionals have clamored for access to Tableau, drastically increasing the number of users.
In order to scale with this growth, Tableau transitioned to a more modern architecture. Multiple instances of Tableau Desktop are no longer installed on individual desktops but instead one instance of Tableau Online lives on a server – either in the company’s datacenter or on the cloud – that users access via web browser. With no need to install or manage software on each desktop, many thousands of employees from a single company can be set up as users and easily access the tool.
However, just like with any move from a client/server application to a web-based application, there was a tradeoff. With the increase in scalability there came a loss in granularity over who is accessing the data. This leads to the critical question: how to govern individual user access to Snowflake data via Tableau?
Users still have individual username and password to access Tableau, but the data itself lives in a separate cloud-based database like Snowflake. Tableau admins have at least two options for configuring the tool’s access to Snowflake:

Ideally, governance and security policies could be configured and managed on the user accounts in Tableau, but that feature isn’t available today. Tableau sees this as a database function. Which brings us full circle back to creating thousands of user accounts in Snowflake in order to govern individual access.
We’ve run into several companies facing this same issue and have developed a unique solution: ALTR can employ contextual info provided by Tableau to distinguish users and apply governance policies on the data in Snowflake. With a simple, one-time configuration of a SQL variable in Tableau server, the service account that Tableau uses to connect to Snowflake can send through information on which one of the thousands of Tableau users is making the request and share that information with ALTR. ALTR can then apply governance and security policy on that Tableau user as it would on any other individual Snowflake account.

And that’s it – there are no additional steps required in Tableau, Snowflake or ALTR. If you're an ALTR customer with Snowflake and you use Tableau server or Tableau online, you can get to this specific level of individual user visibility and governance in less than an hour just by making that one small change.
Without a way to ensure that sensitive and regulated PII data can be monitored and controlled when accessed by BI tools via bulk service accounts, many companies are forced to exclude that data from their analytics tools, leading to a less than 360 view of the business.
ALTR’s solution delivers the best of both worlds: Snowflake DBAs only have to configure and manage the one Tableau Snowflake service account, yet they get per user visibility and governance as if every end user had their own account. This means they can implement access controls, apply masking policies, and stop credentialed access threats on thousands of end users — allowing continued access to data without putting the data at risk. That means companies can include the sensitive data they need in order to get a full view of the business and extract the most value from their data and Snowflake.
And ALTR is the only data governance and security provider for Snowflake delivering this capability. It’s another example of our drive to build SaaS-based functionality that is quick and easy for our customers to deploy while delivering powerful data control and protection.

The Data Governance and Information Quality Conference is just around the corner, and we’re hyped for it! Data Governance has screamed to the top of many priority lists this year as companies adopt the controls they need to get value from data while keeping it safe. It makes sense, as multiple US states now have privacy regulation in place, with US federal privacy laws looming as well. We’re crossing a point where governance tools and processes need to be in place before you can appropriately use data, otherwise your company is at risk of not just data breaches, but the new and increasing regulatory fines that come with them. At DGIQ this year, we’re excited to learn more about the governance standards that are firming up, along with the trends we can expect going into 2022. Below are some of the presentations we’re particularly looking forward to.
This session is all about how organizations can incorporate data governance into their overall data strategy. We look forward to Donna sharing her insights into how effective data governance can actually increase your organization’s ability to get value from data.
Description: In today’s data-driven enterprise, creating a data strategy can seem more complex than ever. Not only is innovation in technology occurring at a more rapid pace than ever before, but as more business stakeholders become involved with data-centric initiatives, “people-centric” initiatives such as data governance increase in importance as well. This workshop demystifies data governance and data strategy and provides practical steps in creating a robust data strategy that encompasses people, process, and technology to provide concrete and demonstrable business value.
Donna Burbank, Managing Director, Global Data Strategy, Ltd.
Be the Match has a noble goal but has to deal with extremely sensitive information in order to achieve that goal. Any healthcare organization can gain some great insights from this session.
Description: Be the Match has an important job to do, we provide cures for blood cancer. Data is at the heart of our mission, but it’s not always easy to see the role that data governance plays in it. In this presentation, we will review how Be the Match is successfully approaching data governance in a way that keeps our life-saving mission at the forefront of our data governance initiatives, and vice versa.
Heidi Perry, Manager, Data Governance & Services, Be the Match
As a side note: joining the donor registry for Be the Match is simple and easy. We’d love it if you considered doing so.
This session discusses the importance of a Data Governance Center of Excellence (COE), and how it can help operationalize DG in your organization. We’re huge fans and look forward to seeing how West Monroe Partners helps their customers implement governance for the long term.
Description: Companies gather data at increasing volume and velocity. Many have realized the need to create a Data and Analytics Center of Excellence. While we recognize there are several key areas of development necessary to achieve this goal, we will focus on key elements to building a successful Data Governance (DG) CoE.
Like any enterprise asset, data needs to be curated with the ideal end state in mind. Standing up a DG CoE early will define organizational needs and reduce downstream challenges. The scope and structure will vary by organization, but the goal is the same: Optimize enterprise data management to maximize value for and empower end-users throughout the organization.
The DG COE should include:
Alice S Huang, Senior Manager, West Monroe Partners
We look forward to seeing you at DGIQ! Be sure to stop by our booth (#18) while you’re there for some fun prizes and giveaways, along with a chance to see some incredible people in person for a change.

We had a great time last week at DGIQ in San Diego! Thanks to everyone who stopped by the booth to chat – it was fantastic to see you all in person! We had some thought-provoking conversations, and we heard some similar themes across those discussions. Many people we spoke to were focused on the process and policy-writing part of data governance, others were just starting their governance journey with a data catalogue, and many more were feeling the pressure from the disruption Snowflake is creating as their companies rapidly move data to the cloud.
Although data governance has been around a while, the industry may be more confusing or bewildering or exciting than ever before. With that in mind, we’ve gathered a few resources to address some of the discussions we had:
While the idea of data governance is not new, how it is defined seems to be shifting as data becomes critical to more companies across every industry. In the past, vendors may have just focused on helping you know about your data: data discovery, data classification and data cataloging. ALTR CEO Dave Sikora has written a couple of posts explaining why just knowing about and cataloguing your data is not enough in today’s regulatory environment. The true end goal has to be keeping sensitive data safe and secure.
Many of the people we spoke to seemed to believe that a data governance journey has to be sequential: you start with data cataloguing, then you write policies that define who gets access to the data and how, then you hand that off to your security team to implement the control and enforcement. But the truth is you don’t necessarily have to go in order and maybe you shouldn’t. What if you could easily find and classify sensitive data, place policy-based controls on it AND start to see how it’s used all at the same time, in one tool? What if seeing how data is used gave you surprising insights that affected the policies you place around it? These blog posts from ALTR’s Pete Martin, Doug Wick, and Paul Franz explain why to consider a different approach and how ALTR can help.
The fast pace of data movement to the cloud has stirred up all kinds of issues, with data governance and security sometimes treated as an afterthought. Teams may think it’s too soon or they’re just getting started. ALTR CTO James Beecham explains why sooner is actually better to make sure you’re getting the most of your cloud data warehouse. And why it doesn’t have to be time-consuming, complicated, costly or slow down the project – embracing a data control and protection solution from the beginning can actually help teams keep up with the speed of their business.
If you didn’t get a chance to stop by the booth and want to hear more, contact us! We’d love to chat.

When many of us think about data security… Oh wait, many of us don’t think about it until there’s an incident or a breaking news story about a breach of our personal data. But if we do, it’s often a mysterious process, accessible only to large enterprises, hidden even from the rest of the company. The data security team is pictured secluded in a dark corner of the office, setting up and monitoring security controls like something out of the Matrix—with tools just as complicated and incomprehensible.
This might have been acceptable when data was only gathered by the largest companies and safely ensconced inside the perimeter of their gigantic data centers. Data security could be centralized and siloed because data was as well. But with the increase in remote work, digital transformation, and the drive to utilize data across businesses of all sizes, sensitive data is now everywhere. And data security must follow. It must come out of the shadows and become accessible to everyone.
While data is a key vulnerability for essentially every company, until recently most companies didn’t want to acknowledge the risk. But now, with a new data breach announcement like the recent Robinhood leak every few weeks, the problem is impossible to ignore. The combination of shadowy data security with the seemingly unending parade of breaches has led to a situation where everyone from users to companies to consumers might feel like it’s impossible to keep data safe.
At the same time, new regulations around data privacy protection keep rolling out. In order to comply with these regulations, companies often run a siloed process where the laws are first interpreted by in-house lawyers or governance teams, then policies are created and handed over to data and/or security teams to implement. End users who actually understand how data needs to be utilized are often left out – rules are imposed from the outside, and enforcement is inscrutable. This can make data users feel cut off from the process of protecting it.
This disjointed, top-down process is the complete opposite of today’s consumer buying experiences. When evaluating a new product or solution, they don’t want to be told – they want to be shown. They expect the opportunity to try things out for themselves and evaluate experiences through their own perspective.
It only makes sense that the same would hold true for business users looking to protect sensitive data. They should have the opportunity to see for themselves how data security solutions work, and even more than that, they should have input into the data governance and control process. Policies should not just be handed down from above and left to be implemented in a black box.
Unfortunately, the traditional buying process for enterprise software, let alone data security, has not been at all transparent. That was one of the big factors in our decision to release the ALTR free plan.
We basically took the traditional software sales model and flipped it on its head. Now, people across the company can try it for themselves: they can implement ALTR on Snowflake for free. They can start to understand how the solution works and also how data is used in their company – what data is accessed and who needs it. Policies can be created collaboratively and organically with input from actual users.
A free version also makes data security available to smaller businesses. Startups and mom and pops know they need business basics like credit card processing and a website, but data security may not be on the “essentials” list. However, even the smallest company now has a mailing list or a loyalty program containing customer PII that should be protected. In fact, it might be even more crucial as the reputational impact of a leak could be even more devastating. We believe data security should be a key component of business culture from the smallest to the largest organizations.
Bringing more users into the process means it’s imperative we make the ALTR solution as easy and intuitive as possible. But it also means guiding users who may be new to data security by providing insights into how data is used and how it needs to be protected.
Some users may know exactly what they want to do, but others might be unsure. Either way you can start with just observing: see who is accessing what data, when and how much. You could think of this like an online banking account. Maybe you log in to pay specific bills, but you may also be interested in how you’re spending your money, looking at expenses grouped by category, and building a budget around that. You can find similar, helpful insights around data usage in ALTR.
In our own product, we see that users are most likely to visit our Analytics feature both before and after viewing their data access policies. In fact, since adding the Heatmap and Analytics to the platform we’ve seen many users dive deep into these features with an uptick in how long users spend on these pages. The close relationship between these pages in the user experience is encouraging us to develop ways to help our users adjust their policies based on what they see in Analytics.
We often hear companies say, “security is everyone’s responsibility.” But how could it be when most of us are left out of the process? Data security should be for all. We wouldn’t accept a world where only the largest homes behind security fences with guards at the gates were safe from break-ins. Today, consumers have access not only to effective window and door locks but also internet-connected cameras. They are now aware when a package is delivered or if there’s a porch pirate snooping around. Why wouldn’t we expect the same visibility and security for our private data?
With the right tools in place, everyone can feel in control and prepared to keep data safe.
Get started with ALTR Free right now.
.png)
One of the first steps organizations take when preparing to deliver a data governance program is to determine where data governance should be placed in the organization. Or in other words, who should own data governance? Kathy Rondon, Chief Business Strategist, R2C, makes a compelling case around who’s responsible for data governance: everyone.
She explained that data will go through stages throughout its lifecycle, starting with Planning, Acquisition/Creation through to Share/Use, and Archive/Dispose. Various roles will touch, modify, and utilize data at each point. The Chief Data Officer (CDO) might be responsible for the overall data lifecycle. At the same time, the Data Owner is responsible for the data produced in their business unit. At the same time, Data Stewards and Data Users might get the most benefit from the information to make their jobs more effective and efficient.
Kathy explained that you can think of this as caring for your child. At various points in a child’s life, there are different caretakers: parents, babysitters, schools, and friends. And each environment might require different protection: a babysitter may need to make sure the child is buckled in for a car ride, and friends may need to watch out for cars when playing outside. Most children don’t have a security guard following them around 24 hours a day, ensuring they’re always safe.
Data governance is the same: it’s not one person’s job; it’s everyone’s. But unfortunately, that can sometimes mean it’s no one’s. Because it doesn’t live with one specific role, data governance can end up as an “orphan,” like a child whose babysitter thinks the parent is picking them up from school that day and parents who feel the babysitter is handling it.
This is similar to something we’ve talked about for a while: Whose Job Is Data Security, Anyway? Like Doug said in his blog, “When responsibility is distributed across various functions, you can end up with an ambiguous, inefficient mess — and serious security gaps.”
To ensure a child is safe, safety needs to be accessible and achievable for everyone responsible: a seatbelt needs to be easily buckled, and all the kids need to look out for cars when playing in the street. Each role must be able to deal with the risks that crop up in their stage.
When it comes to using data security to enforce data governance policies, we need easy tools for everyone to use, buy, spin up, or manage. That’s the point of ALTR’s platform: we simplify data security for everyone in the data lifecycle.

With a SaaS-based, no-code, automated solution, whether you’re a CDO or a Data User, you can purchase and use data security for the section of the data you’re responsible for. You can get what you need to fit your role’s security needs and the outcomes required by your function: Data Owners might care about the analytics and the reporting, while the Data Stewards may need to ensure that the actual policies and locks are correct.
When it’s nobody’s job, securing your slice of the data must be easy. It can’t be cumbersome, it can’t be expensive, and it can’t be slow. Data security has to be as easy as putting on a seat belt.

Companies have embraced the power and scale of enterprise data warehouses (EDWs) for decades, and rightly so. EDWs centralize a wealth of data so that various corporate functions can access it, track business results, and analyze trends to support better decision making.
Unfortunately, traditional on-premises EDWs come with significant overhead in terms of time, money, and effort. You have to set them up, which is complicated enough, and then you have to dedicate IT staff to keep them running. That team will spend all of its time adding servers and storage, configuring software and hardware, tweaking data and queries to play nicely with each other, and so on.
No wonder, then, that organizations are increasingly turning to cloud data warehouses (CDWs). Providers such as Amazon, Google, and Snowflake now make it simple to:
That last point is the real kicker. With EDWs, any change in scale implies serious effort as new equipment is brought online. By contrast, CDWs handle scaling natively, to the point that users almost never need to think about scaling at all.
Other old headaches from EDWs fall by the wayside, too. For example, by decoupling data management from the process of running queries, CDWs allow users to introduce new data without affecting data-crunching jobs that are already in progress. That opens up a whole new world of convenience and efficiency for both administrators and end users.
Yet even the best CDWs can be made stronger when it comes to managing data access. Companies like Snowflake do offer safeguards when it comes to user permissions and protection for at-rest data so that you can rightly feel comfortable about shipping your data to them.
Ultimately, though, the great value delivered by Snowflake, Amazon Redshift, and other CDWs is high performance at a very attractive price. They’re not in the business of supplying locks on the consumption of data, and because their whole infrastructure is virtualized, it’s not workable to implement traditional measures such as data loss prevention (DLP) or endpoint protection around the data stack.
Regulating initial access to a CDW is easy enough thanks to single sign-on (SSO) providers like Okta. Using one of these tools makes it easy for the organization to authenticate remote users before letting them inside the front gate of the CDW.
After that, however, things get slippery from the standpoint of data governance. Who is accessing which data? How much data at a time? When? From where? These are the open questions that every company using CDWs must address.
In a pinch, you might try to fill these gaps by falling back on older technology. For example, you could technically manage access to your CDW by using a proxy. But that would hamper performance, and you might still be vulnerable to certain types of attacks.
The far better approach is to pair the benefits of your CDW with a query-level solution for data security and governance that works in parallel — one that’s abstracted, elastic, and has no infrastructure. That’s where data security as a service (DSaaS) comes in.
By using a last-mile, client-side approach, DSaaS provides data governance without any appreciable impact on performance. Security is usually the #1 offender when it comes to slowing down applications, including any kind of database. But by distributing security across all of the code, DSaaS gives you the most control, the most visibility, and the most context while also allowing you to harness the full flexibility, speed, and scalability of your CDW.
By putting security and governance within the application itself, DSaaS keeps you from getting siloed into an old security paradigm. Whether you want to move to a new data center, or just grant permissions to an old user who has a new laptop, it’s easy to enforce your pre-existing security and governance policies within the CDW. By using DSaaS, you’re able to:
You’ve already given yourself the ultimate flexibility in terms of growth, storage, and computing power by using a CDW. Don’t limit that flexibility and freedom by how you secure access to it, and don’t risk going without data governance in this era of strict data regulations. Take advantage of DSaaS instead. To learn more about DSaaS, check out our latest white paper, Introduction to Data Security as a Service.

As companies aggregate more and more data from multiple data sources into cloud data warehouses in order to remove silos and find insights across disparate data, there can be one big stumbling point: data warehouse security.
This is a problem if the data is so sensitive only a few people in the company should have access to it. This is especially a problem if the data is also so important the company can’t utilize the cloud data platform to its full potential to understand the business without it. That means the data has to be in your cloud data platform—but what if your cloud data warehouse admin isn’t one of the few people in the company who should have access to the data? Then you'll have to ensure that your cloud data warehouse security is up to the task.
Cloud data warehouse admins have virtually unlimited control over a company’s instance. They set up security protocols, they set up users and access, they manage the data flows in and out. You might trust your admin, but can you trust that their credentials will never be stolen or misused?
There are a couple of ways that someone with admin credentials could get access to sensitive data without non-admins being aware:
Scenario 1:
Assume the role of a person who should have access to the data such as a CFO. Because they have the power in the platform to set up and modify user accounts, they could impersonate someone with permission to access the data.
Scenario 2:
Disable platform governance and security controls – views, masking policies and user-defined functions - and access the data directly.
SaaS-based ALTR acts like a neutral third party, providing consumption visibility and data protection that’s natively integrated into to the cloud data platform yet outside the control of the platform admin. This separation of duties is what makes ALTR’'s platform so powerful when it comes to improving data warehouse security of sensitive data in platforms like Snowflake.
While there’s no foolproof way to stop the admin or someone with their credentials from attempting to access the data, ALTR’s unique combination of data rate limiting and data access visibility can reduce the impact and risk of the two scenarios.
ALTR makes it impossible to access the data without key people being notified and can limit the amount of data revealed, even to admins:
See a walk through of this use case:
Effective data warehouse security requires a combination of features unique to ALTR: Delivering real time alerting and limiting risk to data requires both a SaaS-based tool for tokenization that sits outside the cloud data platform PLUS the ability to implement consumption limits on data requests. A data governance tool alone wouldn't solve the problem. It needs a combined data governance and data security solution unique to ALTR.
ALTR's solution for a separation of duty between operation of data and security of data provides a check on the power of platform admins (and their credentials). The most self-aware cloud data platform admins actually want this kind of outside oversight to ensure the data in their charge is kept secure.

Just like every company became a technology company in the early 2000s, every company is now becoming a data company. For effective marketing and sales, for operational efficiency, for financial management - companies that win and companies that leverage data to learn are now one and the same.
Data used to be hidden from view, wrapped inside of applications wrapped inside of bespoke IT infrastructure. Now it's in the Cloud, inside of platforms like Snowflake or Amazon Redshift that put it right at the fingertips of anyone in your company. Massively scalable, cost effective, supported by thousands of ecosystem technologies - the opportunity here is incredible.
Also incredible are the new risks to data. When it's right at the fingertips of everyone in your company, it's more easy for it to be improperly shared or stolen than ever.
Do you focus on the infrastructure? Well, it's not yours anymore so while you can and should configure security over your cloud infrastructure correctly, you will never truly control it.
Do you focus on the people? Identity or attributes of identity work well in small numbers but get incredibly complex at any level of scale, and identities get compromised all of the time.
Don't treat the firewall or the login screen as the endpoint; treat the data as the endpoint.
This approach starts with partners like OneTrust, BigID, and others that help you understand your data and get a handle on how it should be made private and secure in order to comply with an ever-more-complex regulatory environment. You need a big brain to look at all of your data across your whole company and document the needed controls to keep your data-driven enterprise safe.
But you also need to be able to act. Your data risk management brain needs muscle to be able to control every place where sensitive data exists in real-time. This isn't just managing simple access to well-defined datasets but also watching consumption levels, with enough sensitivity to detect activity against data that is unusual and indicative of stolen credentials. This is what we are building at ALTR, and the concept of a unified data control plane across your entire organization that treats data as the endpoint is what animates our product strategy.
Right now it's all about the data - the opportunity and the risks. With the right data-first defensive strategy in place to mitigate those risks, the world of opportunity opens up to you.
To learn more, watch our webinar "The Hidden ROI: Taking a Security-First Approach to Modern Data Architectures".

As a parent, I’m always watching out to keep my kids safe – whether it’s keeping an eye on traffic or watching what they eat. Having been in the cybersecurity industry for some time now, it has led me to be even more concerned about how their personal data is used by those who have access to it. As an example, there was one case where my daughter's pediatrician sent me her test results via his personal Gmail account rather than a corporate one or by a more secure method.
Situations like this are less rare than you might think. The healthcare industry is dealing with inside and outside threats to protected health information (PHI) while trying to utilize data to innovate and improve patient care. In 2020 the industry faced the highest average total cost per breach, increasing 10% from the previous year. The industry desperately needs a better solution to protecting its data.
Ransomware attacks on the healthcare industry increased 60% to 123% in 2020 (depending on the report) with bad actors taking advantage of the disruptions created by the pandemic. These attacks are also increasing in pressure with bad actors not just encrypting data but stealing it as well. This puts increased stress on organizations to pay in order to avoid regulatory consequences for leaked data. Nearly 60% of ransomware attacks that the IBM X-Force responded to in 2020 used what they’re calling a “double extortion strategy” where attackers encrypted, stole and then threatened to expose data if the ransom wasn't paid. Ireland’s nation health service is dealing with this exact issue after hackers broke into the Health Service Executive’s (HSE) IT system in May. The attack not only led to a disruption in services, but personal records of individuals being released online. The same group has targeted at least 16 U.S. health and emergency networks this year.

The increase in threats hasn’t slowed the healthcare industry’s expansion of data sharing and utilization. Data is driving innovation in original medical research, new drug development, improved clinical care, and innovative medical devices. A recent Economist Intelligence Unit survey showed that the healthcare and life sciences industry was most likely to cite data and analytics as a critical factor for success over the next three years. The respondents’ top three priorities were developing new products or services, increasing client satisfaction and experience, and revenue and profit growth. They were also more likely than others to purchase or accept data from both government and non-government agencies. However, the risk of sharing data externally is a top concern with the healthcare industry listing “risk of a leak of confidential information” as number one with 54% of respondents.

This all makes protecting sensitive data more critical than ever. In the past, healthcare organizations may have thought that a full-fledged, time- and resource-intensive Data Loss Prevention (DLP) solution was the only option to truly protect sensitive data. The fact is legacy enterprise DLPs are costly, usually require a long on-premises installation and complex policy rollout, and don’t extend well into the cloud. They tend to put blocks in place that make it more challenging to get important data into the necessary hands. This is less than ideal for an industry that needs to share data to provide the best care and innovate quickly.
Modern cloud-based, no-code solutions like ALTR provide a better alternative by making it easy to automate data access controls, protect data at rest, and respond to threats in real-time. Unlike traditional solutions, ALTR requires no infrastructure to install, maintain or scale, and nothing needs to be placed on the endpoint. And unlike other solutions, ALTR delivers both data governance and data security. Organizations can add data sources, create policy, and respond to potential threats without writing a single line of code. Sensitive data is classified wherever it is, policy enforcement is automated, consumption is visible and controlled, and sensitive data is tokenized to mitigate the risk of exfiltration, while potential threats are handled as they happen. Protection is focused on the data, where it should be.

ALTR customer TULIP is a great example of this use case. The company provides an online platform that allows fertility patients from all over the world to search a proprietary database of nearly 20,000 egg donors to find their perfect match. TULIP turned to ALTR for a data protection service that keeps customer PHI safe and provides a secure audit trail of every request for data.
With a modern data governance and security solution, the healthcare industry can better protect its sensitive information while fully utilizing that data to improve patient outcomes, create better clinical processes, and produce innovative medical treatments and devices that can benefit us all.

Whenever there’s a significant change in technology, quality of life improves dramatically. We’ve experienced these changes three times recently with the industrial (1760), technological (1870), and digital (1950) revolutions. These eras drive rapid new innovations and technologies that improve communication and healthcare, reduce poverty levels and the cost of goods, and ultimately make life better for us all. In just the last 150 years, we’ve seen huge improvements in life expectancy (from an average lifespan of 35 years to 80 years), child mortality (from 43% to 4.5%), and global poverty (From 80% to less than 10%).
We’re now in the middle of a fourth industrial revolution: the data revolution. This new age promises to further improve the way we communicate, how we provide healthcare and education, how we take care of the less fortunate, and how businesses build products. Everyone stands to benefit from the use of data for the greater good. We just have some hurdles to get through first.

We’ve all heard the phrase “data is the new oil”. It signifies that data is being used as fuel to power the economy similar to how oil played such an important role over the last 150 years. Those that don’t use data to its fullest risk being left behind in this new “data age”, and we’ve seen early adopters crop up and dominate with their early use of data at scale - think Facebook and Uber with how effectively they use algorithms in their business models. Unfortunately, there’s a dark side to data as well.
Data, like oil, is valuable but also risky. Just like oil provides fuel to power vehicles, heat buildings, and provide electricity, it also poses significant environmental and business risks when wells and tankers leak into their surroundings. We all recall the events of the Deepwater Horizon oil well and its aftermath, resulting in BP paying over $60 Billion in criminal and civil penalties. BP’s fines set a benchmark that influenced the size of future penalties, with companies like Volkswagen paying $30 Billion for cheating on diesel emission standards.
Data’s value comes in its ability to speed up time to insights so we can make better decisions, faster. It can also enable projects that benefit the public good around the world. However, if done without proper safeguards, we risk reducing the value by leaking private and sensitive information and suffering costly and damaging data breaches. As companies rush to get value from data, we’re seeing a rise in data breaches, associated fines and regulatory penalties. Equifax alone paid more than $550 Million for its 2017 data breach affecting 150 million people, and Amazon is facing the largest ever fine assessed by the EU for a GDPR infraction at $880 million
According to professor and author Ruth DeFries, technological innovation follows a cyclical pattern dubbed Ratchet, Hatchet, Pivot. When a new technology comes out (Ratchet), society takes advantage of it to rapidly move forward, but not without consequences. Then, the hatchet drops as change is demanded to fix the damage caused by these new problems. Finally, a pivot occurs leading to new innovations and a new period of ratcheting up.
Oil has followed this ratchet, hatchet, pivot model. It led to great advancements, but not without serious environmental problems. The hatchet fell as society demanded companies take responsibility for their actions. Environmental regulations and fines were introduced, leading to safer oil production and investments in alternative sources of power. Now, the pivot is here as mainstream companies and investors move toward environmentally friendly power sources like wind and solar (see Mercedes Benz' recent $45 Billion plan to become an all-electric vehicle provider).
In the fourth industrial revolution, data, too, seems to be following this trend. At first, data gave early adopters an advantage in building their businesses, but not without serious consequences to individual privacy. The hatchet has come down here as well, with new privacy regulations in the EU (GDPR), California (CCPA), and recently Virginia and Colorado. In a recent report on GDPR, regulatory fines had risen 40% year over year to $191.5 Million. These fines will increase until society pivots to implementing controls around data to ensure its privacy and security. Once this pivot is made, society will ratchet up once more as we confidently yet safely get value from data.
Data, like oil before it, truly is the fuel driving this next technological revolution. Forward-thinking organizations are using data to make better decisions, faster than ever. However, society is demanding that organizations take steps to safeguard private information. Utilizing data in this new age requires doing so safely, keeping sensitive information protected from privacy and security risks. The alternative is to lock data down completely, limiting its value and positioning your organization on the sidelines as the world moves forward. By implementing proper governance and controls, you can unlock the maximum value from your data while minimizing the risks of regulatory fines and data breaches, allowing your organization to thrive in this new era.

ALTR recently hosted a roundtable with CISOs and IT decision makers to discuss the question “why is data so hard to protect?” This diverse group of participants shared their personal experiences and challenges around keeping data safe with the new struggles remote work brings to the table.
Despite dramatic differences in the attendees’ experience and industry, several common themes emerged around why data is hard to protect:
So, how do you keep data both safe and accessible to those who need it to do their jobs? And how do organizations address these challenges?
To start, it’s difficult to know where all your sensitive data is stored. A recent Information Age study showed that 82% of companies admit to not knowing where their data is located – even sensitive data like personal addresses and banking details. If an organization doesn’t know where the data is stored, then how can they expect to protect it? The ability to observe your data is an absolute must, not only to protect it but to gain insight around how it’s being consumed in order to create policy and to actually utilize its value to become a more data-driven enterprise.
More recently, companies have had no choice but to move toward a remote work model -- that means the traditional strategy of locking down data access on-premise is no longer an option. More remote access means the risk of credentialed access compromises has increased. Now having observability into who is consuming what data, and real-time control over that consumption, becomes ever more critical.
Do you relate to the same concerns that the participants in our roundtable listed? Are you one of the 70% of organizations that are struggling to adapt to this “new normal” in data security (TechRepublic)? Maybe it’s time to chat.